SSH IoT device management AWS has become a pivotal solution for businesses looking to enhance their IoT infrastructure. As the Internet of Things (IoT) continues to grow, so does the need for secure and efficient device management. AWS provides a robust platform that enables users to manage IoT devices effectively while ensuring secure shell (SSH) access for remote connectivity.
In this ever-evolving technological landscape, managing IoT devices securely is no longer optional but a necessity. With SSH IoT device management AWS, organizations can streamline their operations, reduce downtime, and ensure data protection. This article delves deep into the intricacies of SSH IoT device management on AWS, providing actionable insights and practical solutions.
This guide is designed for both beginners and professionals who want to understand how AWS can revolutionize their IoT management strategies. From setting up SSH access to optimizing security protocols, we will cover everything you need to know. Let’s get started!
Table of Contents
- Introduction to SSH IoT Device Management AWS
- The Importance of Secure Shell in IoT
- AWS Services for IoT Device Management
- Setting Up SSH IoT Device Management on AWS
- Security Considerations in SSH IoT Management
- Optimizing SSH IoT Device Management on AWS
- Best Practices for SSH IoT Management
- Troubleshooting Common Issues
- Use Cases for SSH IoT Device Management AWS
- The Future of SSH IoT Device Management AWS
- Conclusion and Next Steps
Introduction to SSH IoT Device Management AWS
SSH IoT device management AWS is a critical component of modern IoT infrastructure. Secure Shell (SSH) provides encrypted communication between devices, ensuring that sensitive data remains protected during transmission. AWS, with its extensive range of services, offers a scalable and reliable platform for managing IoT devices.
In this section, we will explore the basics of SSH and its role in IoT device management. We will also discuss why AWS is the preferred choice for businesses looking to implement SSH-based solutions.
Why Choose AWS for IoT Device Management?
AWS provides several advantages for IoT device management, including:
- Scalability: AWS can handle millions of IoT devices without compromising performance.
- Security: AWS offers advanced security features to protect devices and data.
- Integration: AWS seamlessly integrates with other cloud services, enhancing functionality.
The Importance of Secure Shell in IoT
Secure Shell (SSH) plays a vital role in IoT device management. It ensures that communication between devices is encrypted and secure, preventing unauthorized access and data breaches.
With the increasing number of IoT devices, the risk of cyberattacks also rises. SSH provides an additional layer of security, making it indispensable for IoT infrastructure.
Key Benefits of SSH in IoT
- Data Encryption: SSH encrypts all data transmitted between devices, ensuring confidentiality.
- Authentication: SSH uses strong authentication mechanisms to verify the identity of devices.
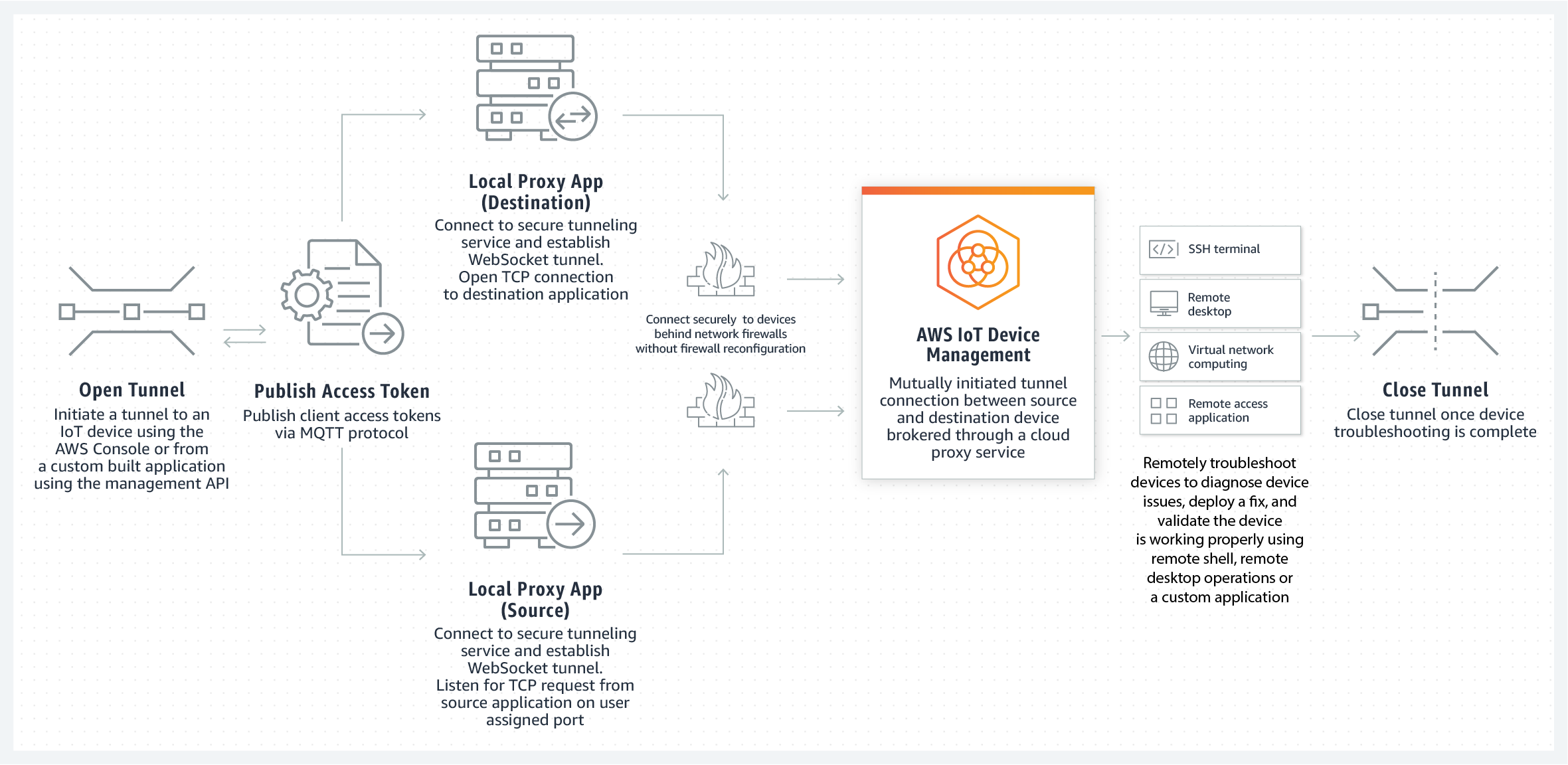
- Remote Access: SSH allows secure remote access to IoT devices, facilitating efficient management.
AWS Services for IoT Device Management
AWS offers a variety of services tailored for IoT device management. These services are designed to simplify the process of setting up, managing, and securing IoT devices.
Key AWS Services for IoT
- AWS IoT Core: A managed cloud service that allows devices to interact securely with cloud applications.
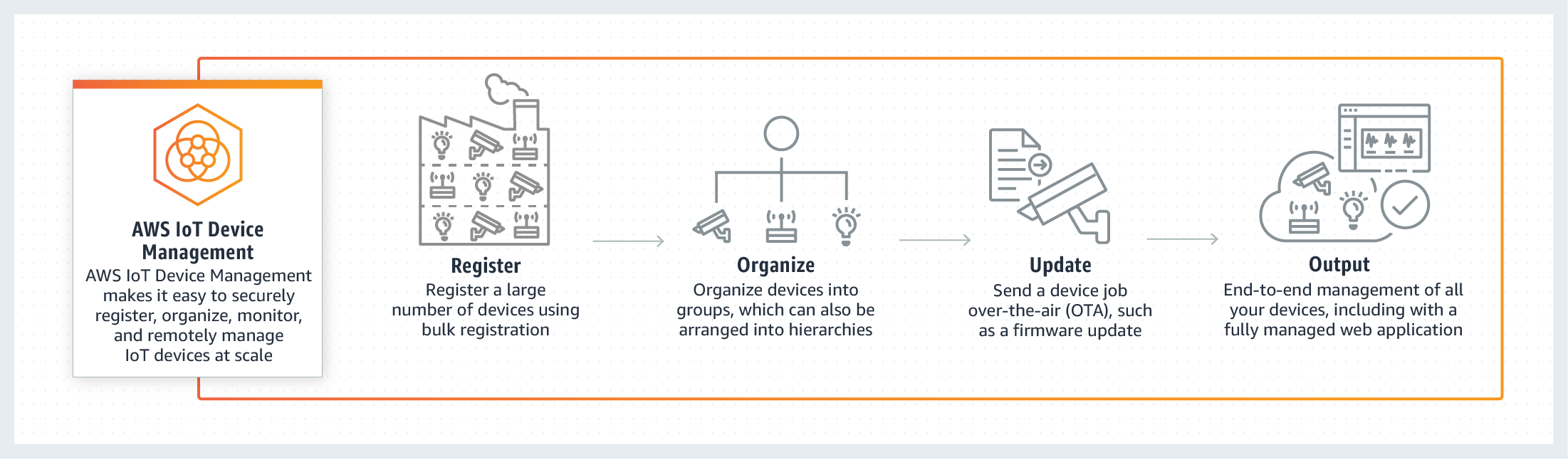
- AWS IoT Device Management: A service that simplifies the process of onboarding, organizing, monitoring, and remotely managing IoT devices.
- AWS IoT Greengrass: A service that extends AWS to edge devices, enabling them to act locally on the data they generate while still using the cloud for management.
Setting Up SSH IoT Device Management on AWS
Setting up SSH IoT device management on AWS involves several steps. From configuring devices to establishing secure connections, each step is crucial for ensuring a smooth and secure setup.
Step-by-Step Guide
- Provision Devices: Register and configure IoT devices on AWS IoT Core.
- Set Up SSH Keys: Generate SSH keys for secure authentication.
- Configure Security Policies: Define security policies to control access to devices.
- Test Connectivity: Verify that devices can communicate securely using SSH.
Security Considerations in SSH IoT Management
Security is paramount when managing IoT devices using SSH. Organizations must implement robust security measures to protect their infrastructure from potential threats.
Best Security Practices
- Use Strong Passwords: Ensure that SSH passwords are complex and unique.
- Enable Two-Factor Authentication: Add an extra layer of security by enabling two-factor authentication.
- Regularly Update Software: Keep all software and firmware up to date to address vulnerabilities.
Optimizing SSH IoT Device Management on AWS
Optimizing SSH IoT device management on AWS can significantly improve performance and efficiency. By following best practices and leveraging AWS tools, organizations can achieve optimal results.
Optimization Techniques
- Monitor Device Performance: Use AWS IoT Device Management to monitor device health and performance.
- Automate Tasks: Automate routine tasks such as updates and maintenance to save time and reduce errors.
- Optimize Resource Usage: Ensure that resources are allocated efficiently to maximize performance.
Best Practices for SSH IoT Management
Implementing best practices for SSH IoT management can help organizations avoid common pitfalls and achieve success. Here are some recommendations:
Key Best Practices
- Document Procedures: Maintain detailed documentation of all procedures and configurations.
- Train Staff: Ensure that staff members are trained in SSH IoT management best practices.
- Regular Audits: Conduct regular audits to identify and address potential security risks.
Troubleshooting Common Issues
Despite best efforts, issues may arise during SSH IoT device management. Knowing how to troubleshoot these issues is essential for maintaining a smooth operation.
Common Issues and Solutions
- Connection Problems: Verify network settings and ensure that SSH keys are correctly configured.
- Authentication Failures: Check SSH keys and passwords for accuracy.
- Performance Issues: Optimize resource allocation and monitor device performance.
Use Cases for SSH IoT Device Management AWS
SSH IoT device management AWS has numerous applications across various industries. Here are some examples:
Industry-Specific Use Cases
- Manufacturing: Monitor and control industrial equipment remotely.
- Healthcare: Manage medical devices securely and efficiently.
- Retail: Optimize inventory management using IoT sensors.
The Future of SSH IoT Device Management AWS
The future of SSH IoT device management AWS looks promising. As technology continues to evolve, AWS is likely to introduce new features and enhancements to its IoT services.
With advancements in artificial intelligence and machine learning, SSH IoT management is expected to become even more intelligent and automated, further improving efficiency and security.
Conclusion and Next Steps
In conclusion, SSH IoT device management AWS is a powerful solution for organizations looking to enhance their IoT infrastructure. By implementing secure and efficient management practices, businesses can reduce risks, improve performance, and drive innovation.
We encourage readers to take the following steps:
- Explore AWS services for IoT device management.
- Implement best practices for SSH IoT management.
- Stay updated with the latest trends and advancements in IoT technology.
Thank you for reading this comprehensive guide on SSH IoT device management AWS. We invite you to share your thoughts and experiences in the comments section below. Feel free to explore other articles on our site for more insights into IoT and cloud computing.