Remote IoT monitoring via SSH is becoming increasingly essential as organizations look to manage and secure their IoT devices from anywhere in the world. With the rise of connected devices, understanding how SSH can be utilized for secure remote monitoring is more important than ever.
In this article, we will explore the importance of remote IoT monitoring via SSH, its benefits, and how it can enhance security and efficiency. Whether you're a beginner or an experienced professional, this guide will provide valuable insights into leveraging SSH for IoT monitoring.
From setting up SSH connections to troubleshooting common issues, this article aims to equip you with the knowledge and tools necessary to implement remote IoT monitoring effectively. Let's dive in!
Table of Contents
- Introduction to Remote IoT Monitoring
- What is SSH?
- Benefits of Using SSH for Remote IoT Monitoring
- How to Set Up SSH for Remote IoT Monitoring
- Securing Your SSH Connection
- Tools for Remote IoT Monitoring with SSH
- Troubleshooting Common SSH Issues
- Best Practices for Remote IoT Monitoring
- Case Studies
- Conclusion
Introduction to Remote IoT Monitoring
Remote IoT monitoring refers to the process of observing, managing, and maintaining IoT devices from a remote location. This is particularly useful for organizations with distributed networks of devices, allowing them to ensure optimal performance and security without physical access.
According to a report by Statista, the number of connected IoT devices worldwide is expected to reach 25.4 billion by 2030. With such a vast number of devices, efficient monitoring solutions are crucial to maintaining system integrity and preventing potential security breaches.
SSH, or Secure Shell, plays a vital role in enabling secure remote access to IoT devices. By encrypting data transmitted between devices and servers, SSH ensures that sensitive information remains protected during remote monitoring activities.
What is SSH?
Understanding SSH Protocol
SSH, or Secure Shell, is a cryptographic network protocol designed to secure data communication, remote command execution, and file transfers between computers. It provides a secure channel over an unsecured network, making it ideal for remote IoT monitoring.
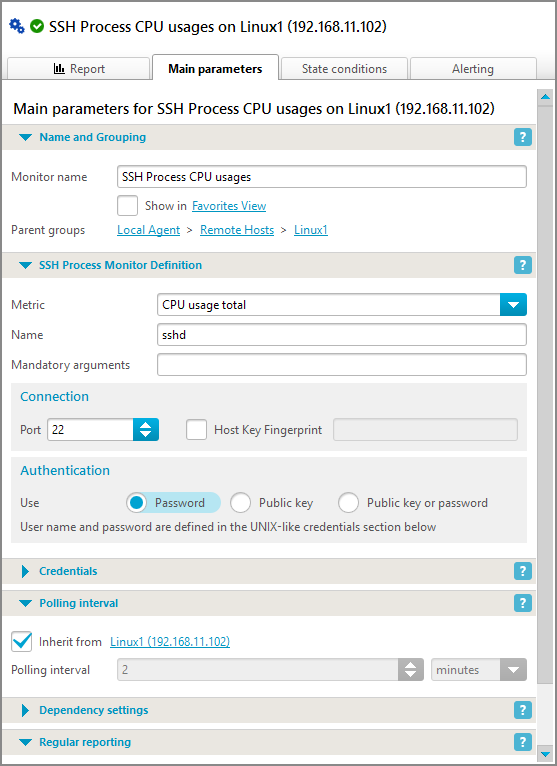
The SSH protocol operates on port 22 by default and supports various authentication methods, including password-based and public-key authentication. This flexibility allows users to choose the most secure and convenient method for their specific needs.
Benefits of Using SSH for Remote IoT Monitoring
Using SSH for remote IoT monitoring offers several advantages, including enhanced security, ease of use, and cost-effectiveness. Below are some of the key benefits:
- Secure Data Transmission: SSH encrypts all data exchanged between devices, ensuring that sensitive information remains confidential.
- Remote Access: With SSH, you can access and manage IoT devices from anywhere in the world, as long as you have an internet connection.
- Automation: SSH enables the automation of routine tasks, such as configuration updates and data backups, saving time and reducing human error.
- Cost-Effective: Implementing SSH for remote monitoring eliminates the need for expensive hardware and travel costs associated with on-site maintenance.
How to Set Up SSH for Remote IoT Monitoring
Step-by-Step Guide
Setting up SSH for remote IoT monitoring involves several steps. Below is a comprehensive guide to help you get started:
- Install SSH Client and Server: Ensure that both the client and server devices have SSH installed. For Linux-based systems, OpenSSH is commonly used.
- Generate SSH Keys: Create a pair of public and private keys for authentication. This enhances security by eliminating the need for passwords.
- Configure Firewall Settings: Allow incoming SSH connections by opening port 22 in your firewall settings.
- Test the Connection: Use the SSH command to connect to the remote device and verify that the setup is functioning correctly.
Securing Your SSH Connection
Best Security Practices
While SSH is inherently secure, additional measures can be taken to further protect your connection. Consider the following best practices:
- Use Strong Passwords: If password-based authentication is used, ensure that passwords are complex and unique.
- Enable Two-Factor Authentication: Add an extra layer of security by requiring two forms of verification for access.
- Disable Root Login: Restrict direct access to the root account to prevent unauthorized access.
- Monitor Logs Regularly: Keep an eye on SSH logs to detect and respond to suspicious activities promptly.
Tools for Remote IoT Monitoring with SSH
Popular Tools and Software
Several tools and software can enhance the remote IoT monitoring experience when used in conjunction with SSH. Some of the most popular options include:
- PuTTY: A free and widely used SSH client for Windows users.
- WinSCP: A graphical SFTP client that allows file transfers over SSH.
- Tera Term: A versatile terminal emulator with built-in SSH support.
- SecureCRT: A professional-grade SSH client offering advanced features and scripting capabilities.
Troubleshooting Common SSH Issues
Solving Connection Problems
Even with proper setup, SSH connections can sometimes encounter issues. Below are some common problems and their solutions:
- Connection Timeout: Check your network settings and ensure that the remote device is reachable.
- Authentication Failure: Verify that your SSH keys or passwords are correct and that the server's configuration allows the chosen authentication method.
- Port Conflict: Ensure that no other services are using port 22 and consider changing the default port if necessary.
Best Practices for Remote IoT Monitoring
Maximizing Efficiency and Security
To make the most out of remote IoT monitoring via SSH, adhere to the following best practices:
- Regular Updates: Keep your SSH client and server software up to date to protect against vulnerabilities.
- Limit Access: Restrict SSH access to only authorized personnel and devices.
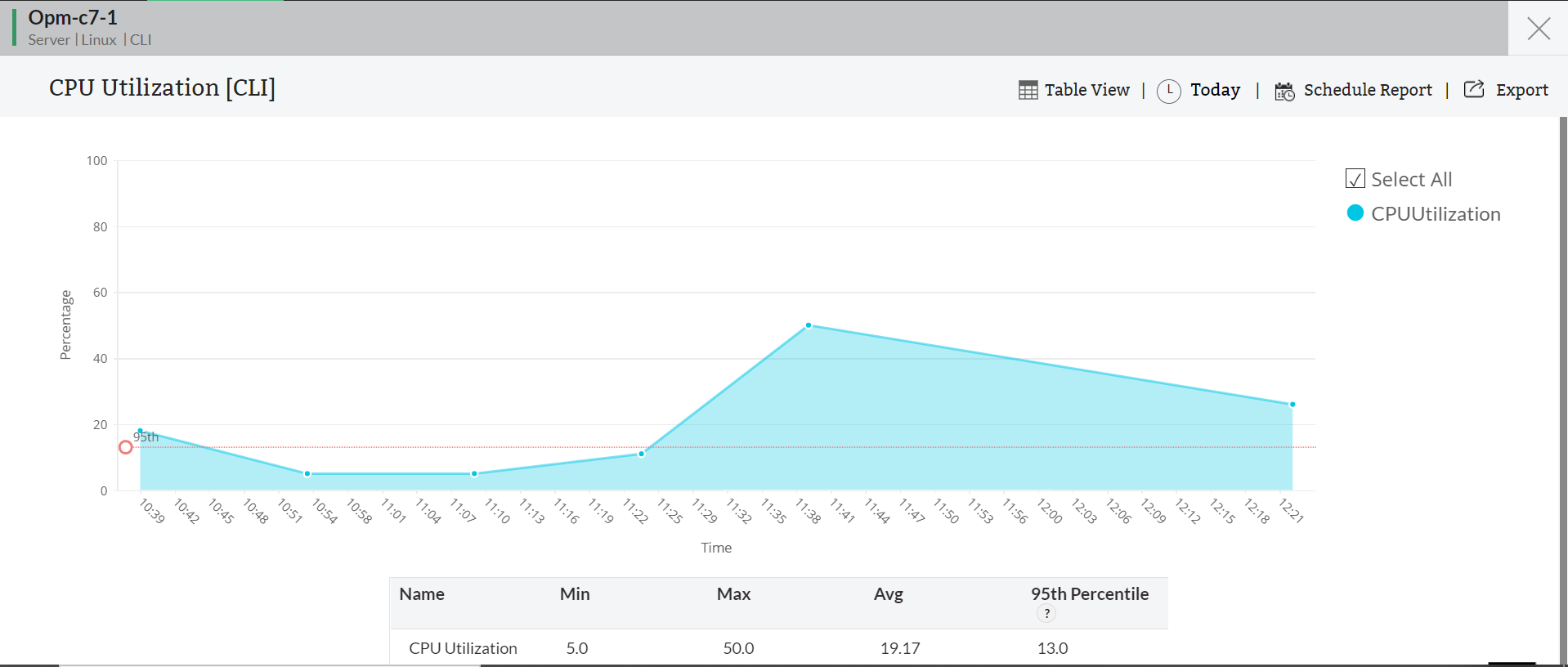
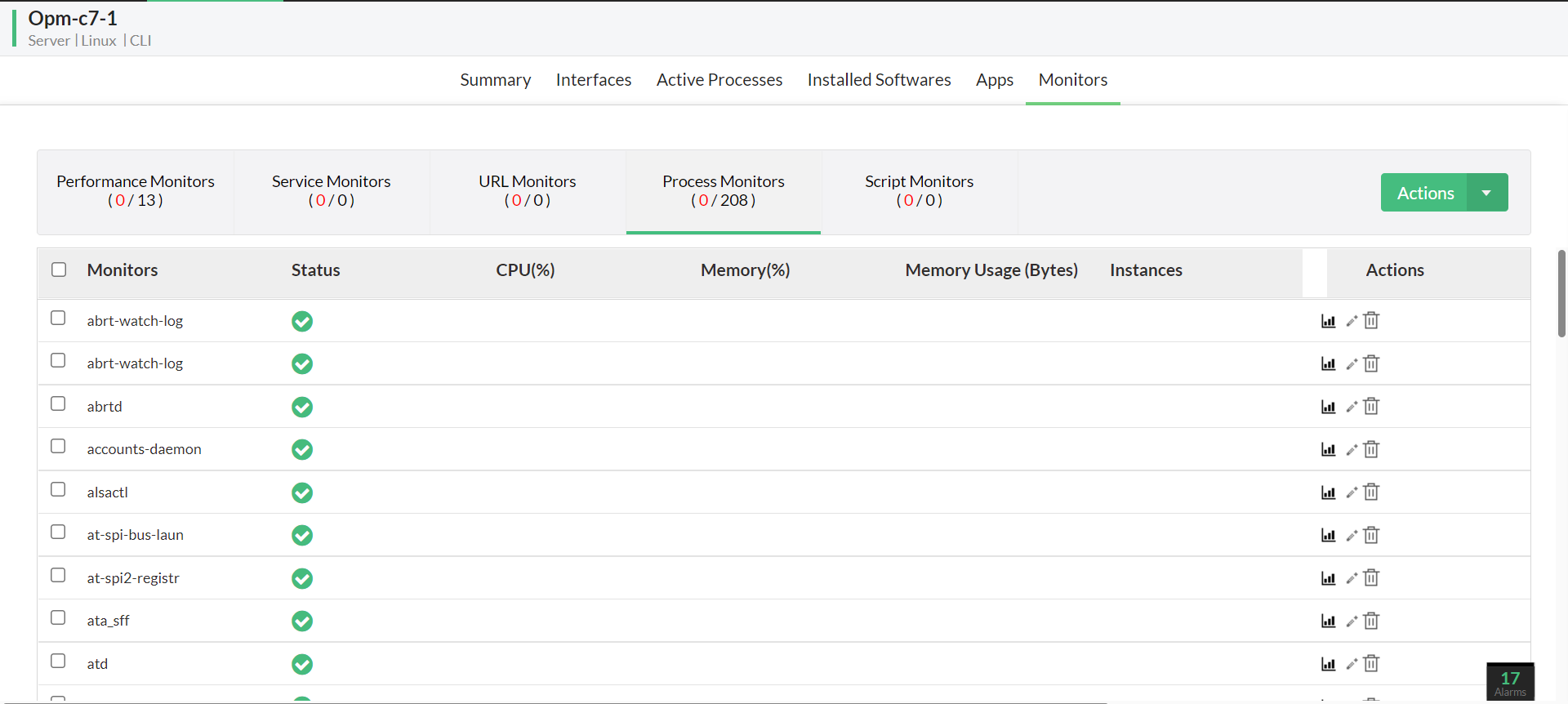
- Monitor Performance: Continuously track the performance of your IoT devices to identify and address issues proactively.
Case Studies
Real-World Applications
Several organizations have successfully implemented remote IoT monitoring via SSH. Below are a couple of case studies highlighting their experiences:
Case Study 1: A manufacturing company used SSH to monitor and manage their IoT-enabled machinery remotely. This resulted in a 30% reduction in downtime and significant cost savings.
Case Study 2: A utility provider implemented SSH-based remote monitoring for their smart grid infrastructure. The solution improved operational efficiency and enhanced the reliability of their services.
Conclusion
Remote IoT monitoring via SSH is a powerful tool for managing and securing IoT devices from anywhere in the world. By following the guidelines outlined in this article, you can effectively implement and optimize SSH for your remote monitoring needs.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more insights into IoT and related technologies.
Data and statistics used in this article are sourced from reputable publications such as Statista and industry reports. For further reading, consider exploring these references to deepen your understanding of remote IoT monitoring and SSH.