In the rapidly evolving world of technology, the integration of Internet of Things (IoT) devices into everyday life is becoming increasingly common. However, with this convenience comes the need for robust security measures. One such measure is the use of RemoteIoT firewalls, which play a critical role in safeguarding IoT networks. Understanding remoteIoT firewall examples can help organizations and individuals strengthen their cybersecurity posture.
As IoT devices continue to proliferate, the risks associated with cyber threats also rise. RemoteIoT firewalls act as a crucial line of defense, protecting these devices from unauthorized access and malicious attacks. By implementing remoteIoT firewall examples, businesses and individuals can better secure their networks and data.
This article delves into various aspects of remoteIoT firewalls, including their functionality, benefits, and practical examples. We will also explore the importance of integrating these firewalls into IoT systems to ensure comprehensive security. Whether you're a tech enthusiast or a professional seeking advanced knowledge, this guide will provide valuable insights into remoteIoT firewall technology.
Table of Contents
- Introduction to RemoteIoT Firewalls
- Importance of RemoteIoT Firewalls
- Key Components of RemoteIoT Firewalls
- Examples of RemoteIoT Firewalls
- Benefits of Using RemoteIoT Firewalls
- Best Practices for Implementing RemoteIoT Firewalls
- Security Challenges Addressed by RemoteIoT Firewalls
- Future Trends in RemoteIoT Firewalls
- Case Studies of RemoteIoT Firewall Implementation
- Conclusion and Next Steps
Introduction to RemoteIoT Firewalls
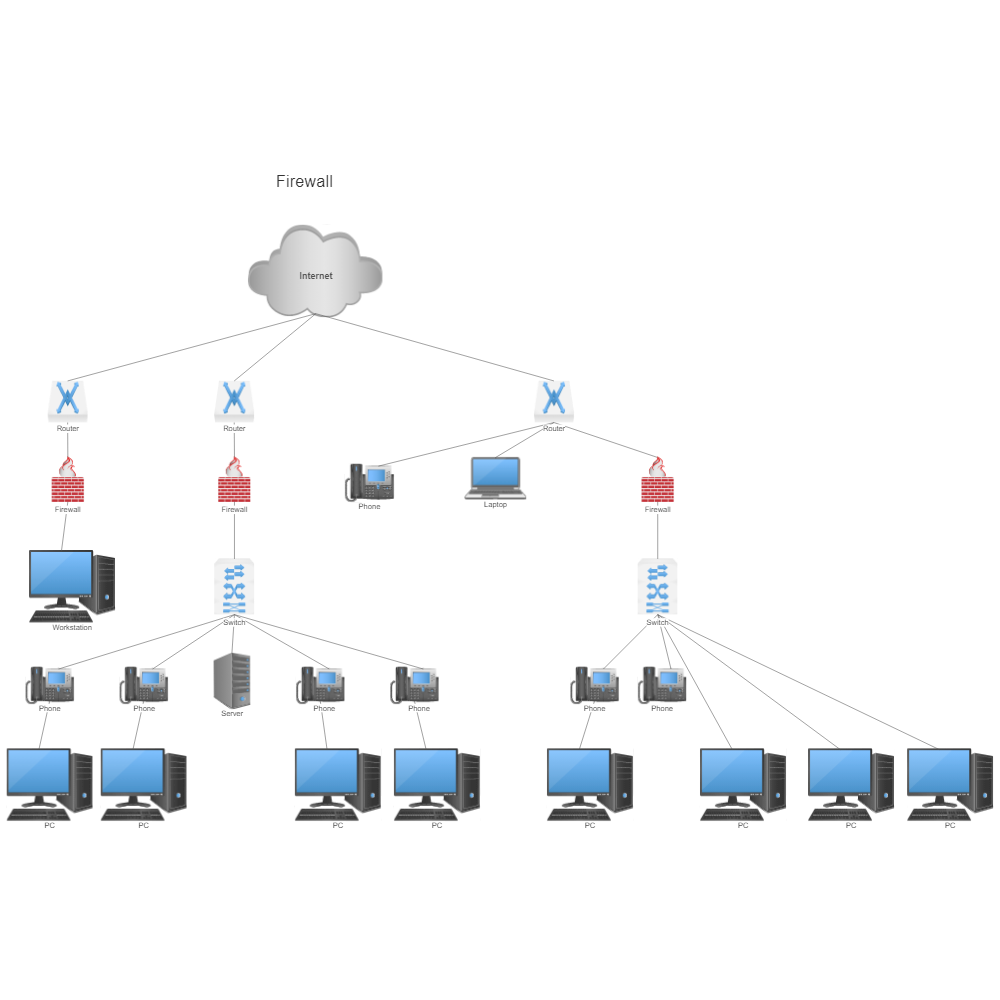
RemoteIoT firewalls are specialized security solutions designed to protect IoT devices and networks from external threats. These firewalls operate by filtering incoming and outgoing network traffic based on predetermined security rules. The primary goal of remoteIoT firewalls is to ensure that only authorized traffic is allowed to pass through, thereby safeguarding the integrity and confidentiality of IoT systems.
RemoteIoT firewalls differ from traditional firewalls in that they are specifically tailored to address the unique security challenges posed by IoT devices. These devices often have limited computational resources and operate in diverse environments, making them more vulnerable to attacks. By deploying remoteIoT firewall examples, organizations can mitigate these risks and enhance overall network security.
How RemoteIoT Firewalls Work
RemoteIoT firewalls employ a combination of techniques to secure IoT networks. These include:
- Packet filtering: Examining individual packets of data to determine whether they should be allowed or blocked.
- Stateful inspection: Monitoring the state of active connections to ensure that traffic adheres to established protocols.
- Intrusion detection and prevention: Identifying and neutralizing potential threats in real-time.
Importance of RemoteIoT Firewalls
As IoT devices become more prevalent, the need for effective security measures becomes increasingly critical. RemoteIoT firewalls serve as a vital component of any comprehensive IoT security strategy. By implementing remoteIoT firewall examples, organizations can:
- Reduce the risk of data breaches and unauthorized access.
- Protect sensitive information from cyber threats.
- Ensure compliance with industry regulations and standards.
Furthermore, remoteIoT firewalls help maintain the reliability and performance of IoT networks by preventing malicious traffic from overwhelming system resources.
Key Components of RemoteIoT Firewalls
A typical remoteIoT firewall consists of several key components that work together to provide robust security. These include:
- Firewall engine: The core component responsible for enforcing security policies.
- Management interface: A user-friendly interface for configuring and monitoring the firewall.
- Reporting and analytics tools: Features that provide insights into network activity and potential security threats.
Understanding these components is essential for effectively deploying and managing remoteIoT firewalls.
Examples of RemoteIoT Firewalls
There are numerous remoteIoT firewall examples available, each offering unique features and capabilities. Some popular options include:
- pfSense: An open-source firewall solution that provides advanced security features for IoT networks.
- OPNsense: A user-friendly firewall platform that supports a wide range of IoT devices and applications.
- Untangle: A comprehensive firewall solution that combines multiple security modules for enhanced protection.
These examples demonstrate the diversity and flexibility of remoteIoT firewall technology, enabling organizations to choose the best solution for their specific needs.
Comparison of RemoteIoT Firewall Examples
When selecting a remoteIoT firewall, it's important to consider factors such as ease of use, scalability, and cost. Below is a comparison of three popular remoteIoT firewall examples:
| Firewall | Features | Cost | Scalability |
|---|---|---|---|
| pfSense | Open-source, customizable, strong community support | Free (open-source) | Highly scalable |
| OPNsense | User-friendly interface, regular updates, strong plugin ecosystem | Free (open-source) | Moderate scalability |
| Untangle | Comprehensive security suite, easy to configure, excellent support | Paid (commercial) | Highly scalable |
Benefits of Using RemoteIoT Firewalls
Implementing remoteIoT firewalls offers several key benefits, including:
- Enhanced security: Protects IoT devices and networks from a wide range of cyber threats.
- Improved performance: Optimizes network traffic to ensure efficient operation of IoT systems.
- Cost savings: Reduces the likelihood of costly data breaches and downtime.
By leveraging these benefits, organizations can achieve greater peace of mind and focus on their core business objectives.
Best Practices for Implementing RemoteIoT Firewalls
To maximize the effectiveness of remoteIoT firewalls, it's important to follow best practices. These include:
- Regularly updating firewall software and firmware to address emerging threats.
- Implementing strong access controls to restrict unauthorized access.
- Monitoring network activity to detect and respond to potential security incidents.
By adhering to these practices, organizations can ensure that their remoteIoT firewalls remain effective over time.
Security Challenges Addressed by RemoteIoT Firewalls
RemoteIoT firewalls address a variety of security challenges, including:
- Unauthorized access: Prevents unauthorized users from gaining access to IoT devices and networks.
- Malware attacks: Detects and blocks malicious software designed to compromise IoT systems.
- Data breaches: Protects sensitive information from being exposed or stolen.
By tackling these challenges, remoteIoT firewalls help organizations maintain the security and integrity of their IoT infrastructure.
Future Trends in RemoteIoT Firewalls
As technology continues to evolve, so too will the capabilities of remoteIoT firewalls. Some emerging trends in this field include:
- Artificial intelligence and machine learning: Enhancing threat detection and response capabilities.
- Cloud-based solutions: Providing greater flexibility and scalability for remoteIoT firewalls.
- Integration with other security tools: Enabling more comprehensive protection for IoT networks.
These trends highlight the ongoing innovation and development in the field of remoteIoT firewall technology.
Case Studies of RemoteIoT Firewall Implementation
Several organizations have successfully implemented remoteIoT firewalls to enhance their cybersecurity. For example:
- Case Study 1: A manufacturing company deployed a remoteIoT firewall to secure its industrial IoT devices, resulting in a significant reduction in cyber threats.
- Case Study 2: A healthcare provider implemented a remoteIoT firewall to protect patient data transmitted through IoT devices, ensuring compliance with HIPAA regulations.
These case studies demonstrate the real-world impact of remoteIoT firewalls in various industries.
Conclusion and Next Steps
RemoteIoT firewalls are essential tools for securing IoT devices and networks. By understanding remoteIoT firewall examples and best practices, organizations can effectively protect their systems from cyber threats. To further enhance your knowledge, consider exploring additional resources and staying informed about the latest developments in remoteIoT firewall technology.
We invite you to take action by:
- Leaving a comment with your thoughts or questions about remoteIoT firewalls.
- Sharing this article with others who may benefit from its insights.
- Exploring other articles on our site to learn more about IoT security and related topics.
Together, we can build a safer and more secure digital future for everyone.