In today's rapidly evolving digital landscape, remoteIoT monitoring SSH has become an essential tool for managing and securing IoT devices effectively. As more businesses and individuals adopt IoT technology, the need for secure and reliable remote access solutions grows exponentially. This article provides a comprehensive guide to understanding remoteIoT monitoring SSH, its benefits, and how to download free tools for Mac users.
With the increasing reliance on interconnected devices, ensuring robust security measures is no longer optional but a necessity. RemoteIoT monitoring SSH offers a secure way to manage and monitor IoT devices from anywhere, making it an invaluable asset for professionals and hobbyists alike.
This article is designed to cater to both beginners and advanced users, offering detailed insights into remoteIoT monitoring SSH, its applications, and practical tips for downloading and setting up free tools on a Mac. By the end of this guide, you will have a clear understanding of how to leverage this technology for your IoT projects.
Understanding RemoteIoT Monitoring SSH
What is RemoteIoT Monitoring SSH?
RemoteIoT monitoring SSH refers to the practice of using Secure Shell (SSH) protocols to remotely monitor and manage IoT devices. SSH is a cryptographic network protocol that ensures secure communication between devices over unsecured networks. It is widely used for remote command-line operations and file transfers.
SSH provides a secure tunnel for communication, encrypting all data exchanged between the client and server. This makes it an ideal choice for managing IoT devices that are often deployed in remote locations or across different networks.
For Mac users, there are several free SSH clients available that can be used to establish secure connections with IoT devices. These tools are user-friendly and offer a range of features to facilitate efficient remote management.
Why Use RemoteIoT Monitoring SSH?
There are several compelling reasons why remoteIoT monitoring SSH should be a part of your IoT management strategy:
- Enhanced Security: SSH encrypts all data transmitted between devices, protecting sensitive information from unauthorized access.
- Remote Access: With SSH, you can manage IoT devices from anywhere, eliminating the need for physical access.
- Automation: SSH allows for the automation of repetitive tasks, saving time and increasing efficiency.
- Scalability: SSH can handle large numbers of devices, making it suitable for both small-scale and enterprise-level IoT deployments.
By leveraging remoteIoT monitoring SSH, you can ensure the security and reliability of your IoT infrastructure while maintaining flexibility and control.
Downloading Free SSH Tools for Mac
Top Free SSH Clients for Mac
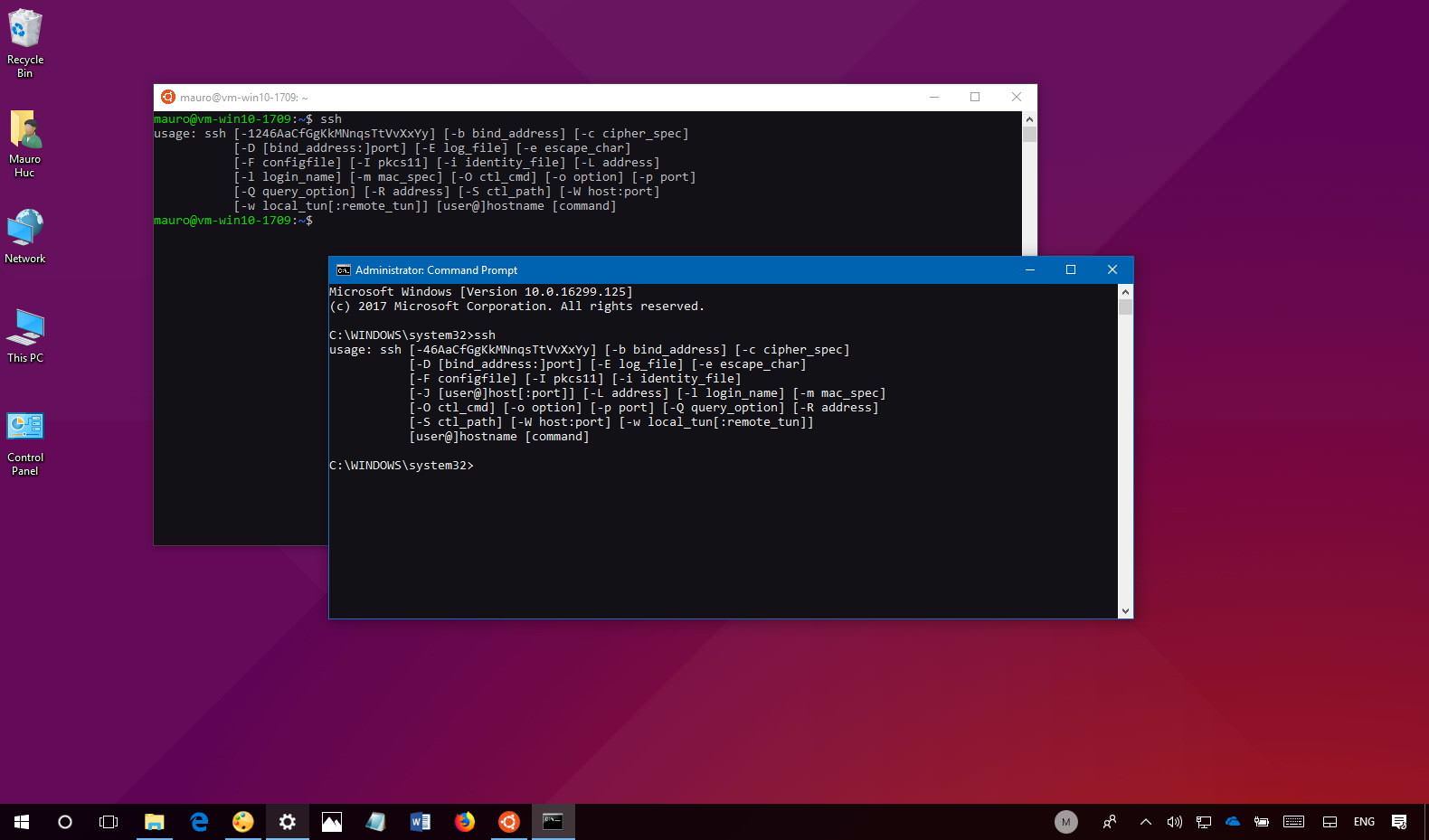
There are several free SSH clients available for Mac users. Below are some of the most popular options:
- Terminal: Mac's built-in Terminal application supports SSH functionality out of the box. It is a powerful and versatile tool for experienced users.
- Termius: A user-friendly SSH client that offers a graphical interface, making it ideal for beginners. It supports multiple connections and has a free version available.
- PuTTY (for Mac): Although originally designed for Windows, PuTTY is now available for Mac users. It is a lightweight and efficient SSH client that is widely used in the tech community.
Each of these tools has its own strengths and weaknesses, so it's important to choose the one that best suits your needs.
Setting Up SSH on Mac
Step-by-Step Guide to Configuring SSH
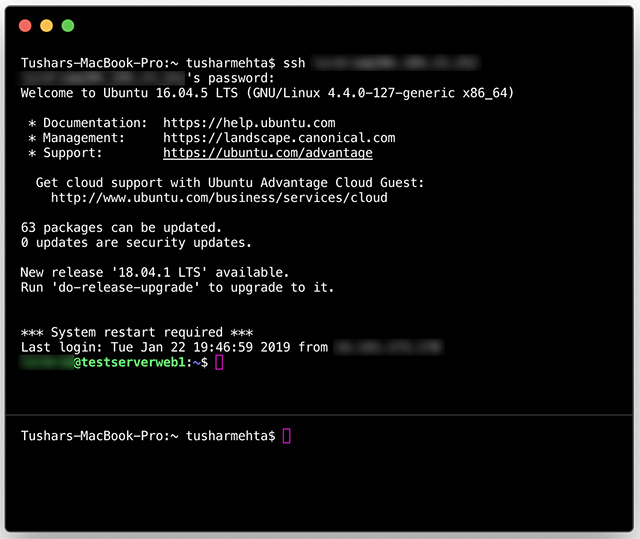
Configuring SSH on a Mac is a straightforward process. Follow these steps to set up SSH for remoteIoT monitoring:
- Open Terminal: Launch the Terminal application from the Utilities folder in Applications.
- Generate SSH Keys: Use the command "ssh-keygen" to generate a public and private key pair. This ensures secure authentication without the need for passwords.
- Copy Public Key: Copy the public key to the IoT device using the "ssh-copy-id" command. This allows the Mac to establish a secure connection without prompting for a password.
- Test Connection: Use the "ssh" command followed by the device's IP address to establish a connection. If everything is set up correctly, you should be able to access the device without entering a password.
By following these steps, you can ensure a secure and seamless connection between your Mac and IoT devices.
Best Practices for RemoteIoT Monitoring SSH
Ensuring Security and Efficiency
To get the most out of remoteIoT monitoring SSH, it's important to follow best practices:
- Use Strong Passwords: Although SSH keys are recommended, if you must use passwords, ensure they are strong and unique.
- Regular Updates: Keep your SSH client and IoT devices up to date with the latest security patches and firmware updates.
- Monitor Logs: Regularly review SSH logs to detect and respond to any suspicious activity.
- Limit Access: Restrict SSH access to trusted users and devices to minimize the risk of unauthorized access.
By adhering to these best practices, you can enhance the security and efficiency of your remoteIoT monitoring SSH setup.
Applications of RemoteIoT Monitoring SSH
Real-World Use Cases
RemoteIoT monitoring SSH has a wide range of applications across various industries:
- Smart Homes: Monitor and control smart home devices such as thermostats, security cameras, and lighting systems from anywhere.
- Industrial IoT: Manage and maintain industrial IoT devices used in manufacturing, agriculture, and logistics.
- Healthcare: Monitor medical devices and patient data remotely, ensuring timely interventions and improved patient outcomes.
These applications demonstrate the versatility and importance of remoteIoT monitoring SSH in modern technology ecosystems.
Common Challenges and Solutions
Troubleshooting SSH Connections
While SSH is a reliable protocol, issues can arise. Below are some common challenges and their solutions:
- Connection Refused: Ensure the SSH server is running on the IoT device and that the firewall allows incoming SSH connections.
- Authentication Failure: Verify that the SSH keys are correctly configured and that the username and password are correct.
- Timeout Errors: Check the network connection and ensure there are no routing issues between the Mac and IoT device.
By addressing these challenges promptly, you can maintain a stable and secure SSH connection for remoteIoT monitoring.
Future Trends in RemoteIoT Monitoring SSH
Innovations and Advancements
The field of remoteIoT monitoring SSH is continually evolving, with several trends shaping its future:
- Quantum Cryptography: As quantum computing advances, new cryptographic methods will be developed to enhance SSH security.
- AI Integration: Artificial intelligence will play a larger role in automating and optimizing SSH processes, improving efficiency and reducing human error.
- 5G Connectivity: The widespread adoption of 5G networks will enable faster and more reliable SSH connections, even in remote locations.
These trends highlight the dynamic nature of remoteIoT monitoring SSH and its potential to revolutionize IoT management.
Conclusion
In conclusion, remoteIoT monitoring SSH is a powerful tool for managing and securing IoT devices. By understanding its capabilities, downloading the right tools, and following best practices, you can harness its full potential to enhance your IoT projects. Whether you're a beginner or an experienced professional, this guide has provided you with the knowledge and resources to get started.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more insights into IoT technology and its applications. Together, let's build a secure and connected future!
Table of Contents
- Understanding RemoteIoT Monitoring SSH
- Why Use RemoteIoT Monitoring SSH?
- Downloading Free SSH Tools for Mac
- Setting Up SSH on Mac
- Best Practices for RemoteIoT Monitoring SSH
- Applications of RemoteIoT Monitoring SSH
- Common Challenges and Solutions
- Future Trends in RemoteIoT Monitoring SSH
- Conclusion