IoT devices are revolutionizing the way we interact with technology, but their security remains a pressing concern. Firewalls play a critical role in safeguarding these devices from cyber threats. As the number of connected devices continues to grow, understanding how firewalls work in IoT environments is more important than ever. In this guide, we will explore everything you need to know about firewall IoT devices and how they protect your network.
With the rapid expansion of the Internet of Things (IoT), more devices are connecting to the internet than ever before. From smart thermostats to wearable fitness trackers, IoT devices offer convenience and efficiency. However, they also introduce new vulnerabilities that cybercriminals can exploit. This is where firewalls come into play, acting as a robust line of defense against unauthorized access and malicious attacks.
This article will delve into the world of firewall IoT devices, explaining their importance, functionality, and implementation. Whether you're a tech enthusiast, a business owner, or a homeowner, this guide will equip you with the knowledge to secure your IoT ecosystem effectively.
Table of Contents
- Introduction to IoT
- What is a Firewall?
- Importance of Firewall IoT Devices
- Types of IoT Firewalls
- How to Configure IoT Firewalls
- Best Practices for IoT Security
- Common IoT Security Threats
- Advantages of Using IoT Firewalls
- Choosing the Right IoT Firewall
- Future of IoT Firewalls
Introduction to IoT
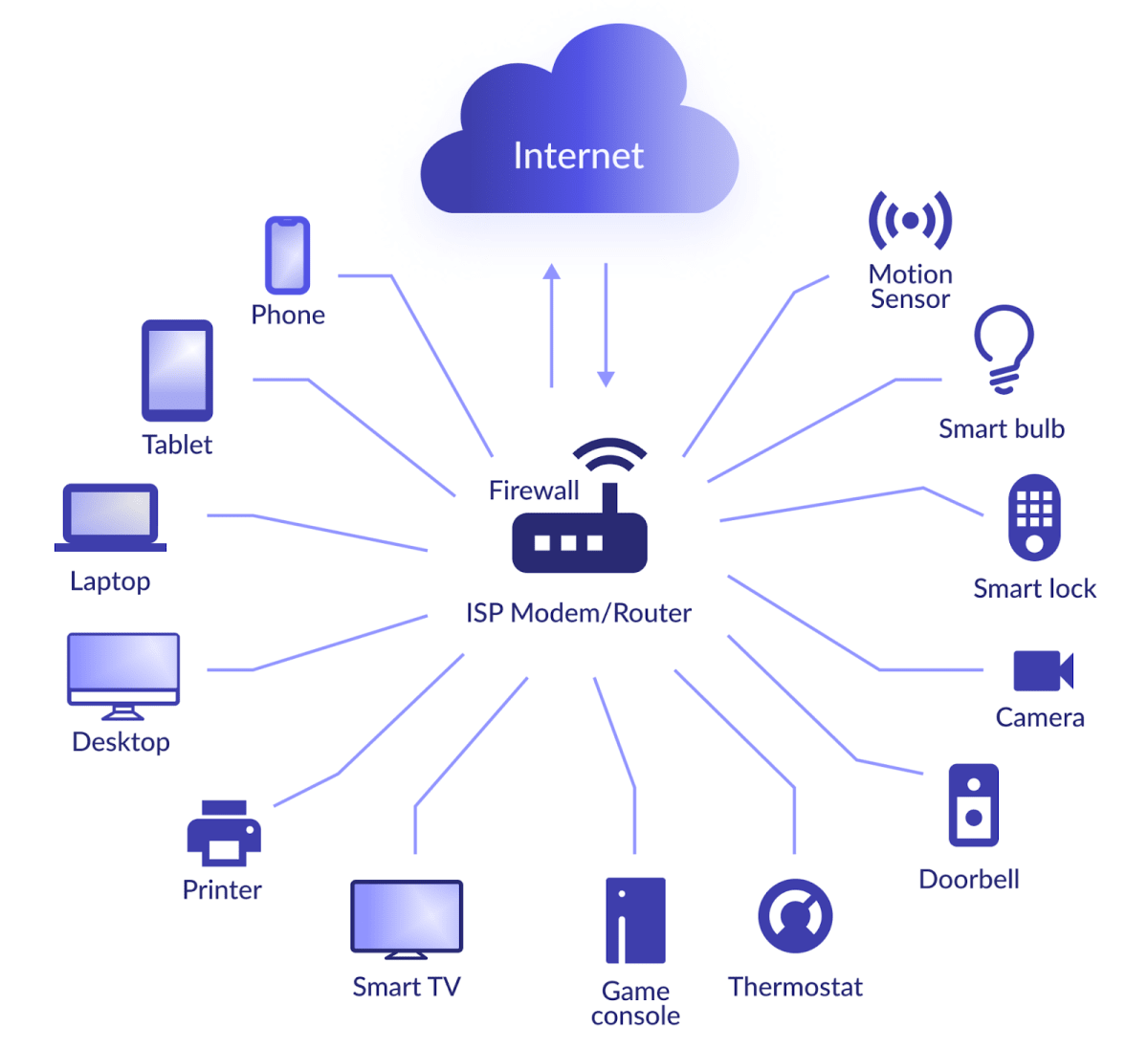
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity that enable them to exchange data. These devices range from smart home appliances to industrial machinery, all designed to enhance automation and efficiency. However, the interconnected nature of IoT devices also makes them susceptible to cyberattacks.
IoT devices often lack robust security measures, making them attractive targets for hackers. This vulnerability underscores the need for comprehensive security solutions, such as firewalls, to protect these devices and the networks they connect to.
What is a Firewall?
A firewall is a security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. Firewalls act as a barrier between trusted and untrusted networks, preventing unauthorized access while allowing legitimate communication. In the context of IoT devices, firewalls play a crucial role in safeguarding the network from potential threats.
How Firewalls Work
Firewalls use various techniques to filter traffic, including:
- Packet Filtering: Examining individual packets of data and allowing or blocking them based on specific criteria.
- Stateful Inspection: Monitoring active connections and ensuring that incoming traffic corresponds to existing sessions.
- Application-Level Filtering: Analyzing data at the application layer to block malicious activities.
Importance of Firewall IoT Devices
Firewall IoT devices are essential for protecting the growing number of connected devices in homes and businesses. Without proper security measures, IoT devices can become entry points for cybercriminals to infiltrate networks and steal sensitive information.
Implementing firewalls for IoT devices helps mitigate risks by:
- Preventing unauthorized access to the network.
- Blocking malicious traffic and potential threats.
- Ensuring the integrity and confidentiality of data.
Types of IoT Firewalls
There are several types of firewalls designed to secure IoT devices, each with its own advantages and limitations:
Hardware Firewalls
Hardware firewalls are physical devices installed between the network and the internet. They provide a dedicated layer of security for IoT devices and are often used in enterprise environments.
Software Firewalls
Software firewalls are applications installed on individual devices or servers. They offer flexibility and customization options, making them suitable for smaller networks or specific devices.
Cloud-Based Firewalls
Cloud-based firewalls are hosted on remote servers and offer scalable solutions for securing IoT devices. They are ideal for organizations with distributed networks or those requiring advanced threat detection capabilities.
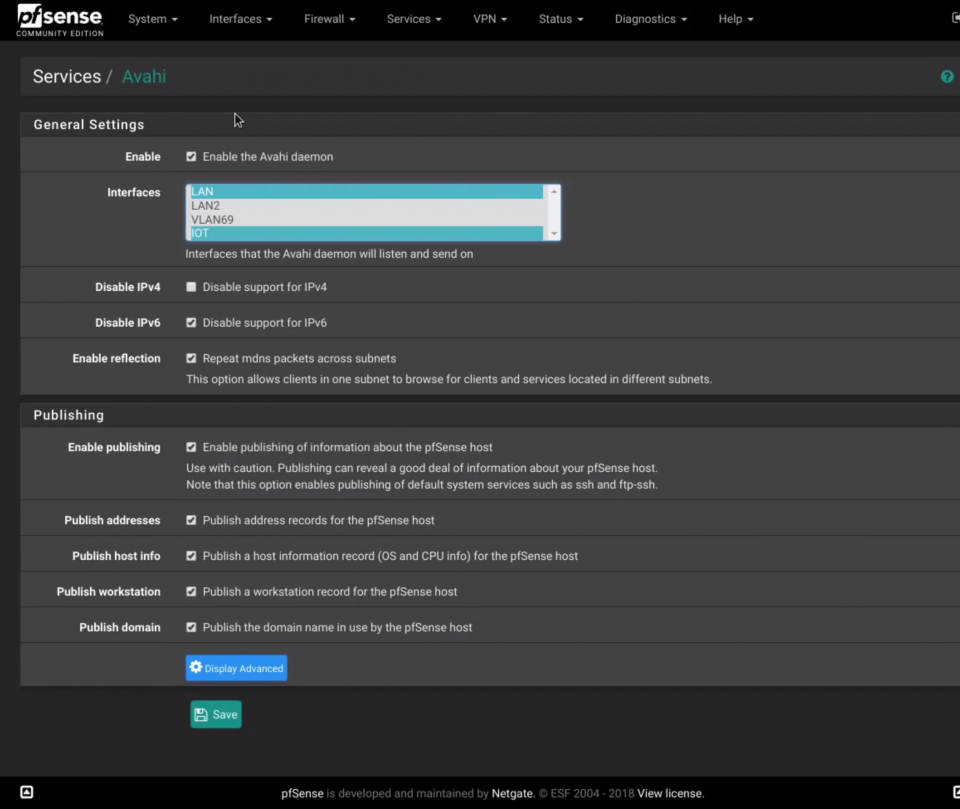
How to Configure IoT Firewalls
Configuring a firewall for IoT devices involves several steps to ensure optimal security:
- Identify Critical Devices: Determine which IoT devices require firewall protection based on their sensitivity and importance.
- Set Security Rules: Establish rules for incoming and outgoing traffic, specifying which connections are allowed or blocked.
- Monitor Traffic: Regularly review firewall logs to detect and respond to suspicious activities.
- Update Regularly: Keep the firewall software up to date to address newly discovered vulnerabilities.
Best Practices for IoT Security
In addition to using firewalls, there are several best practices for securing IoT devices:
- Change Default Credentials: Replace default usernames and passwords with strong, unique ones.
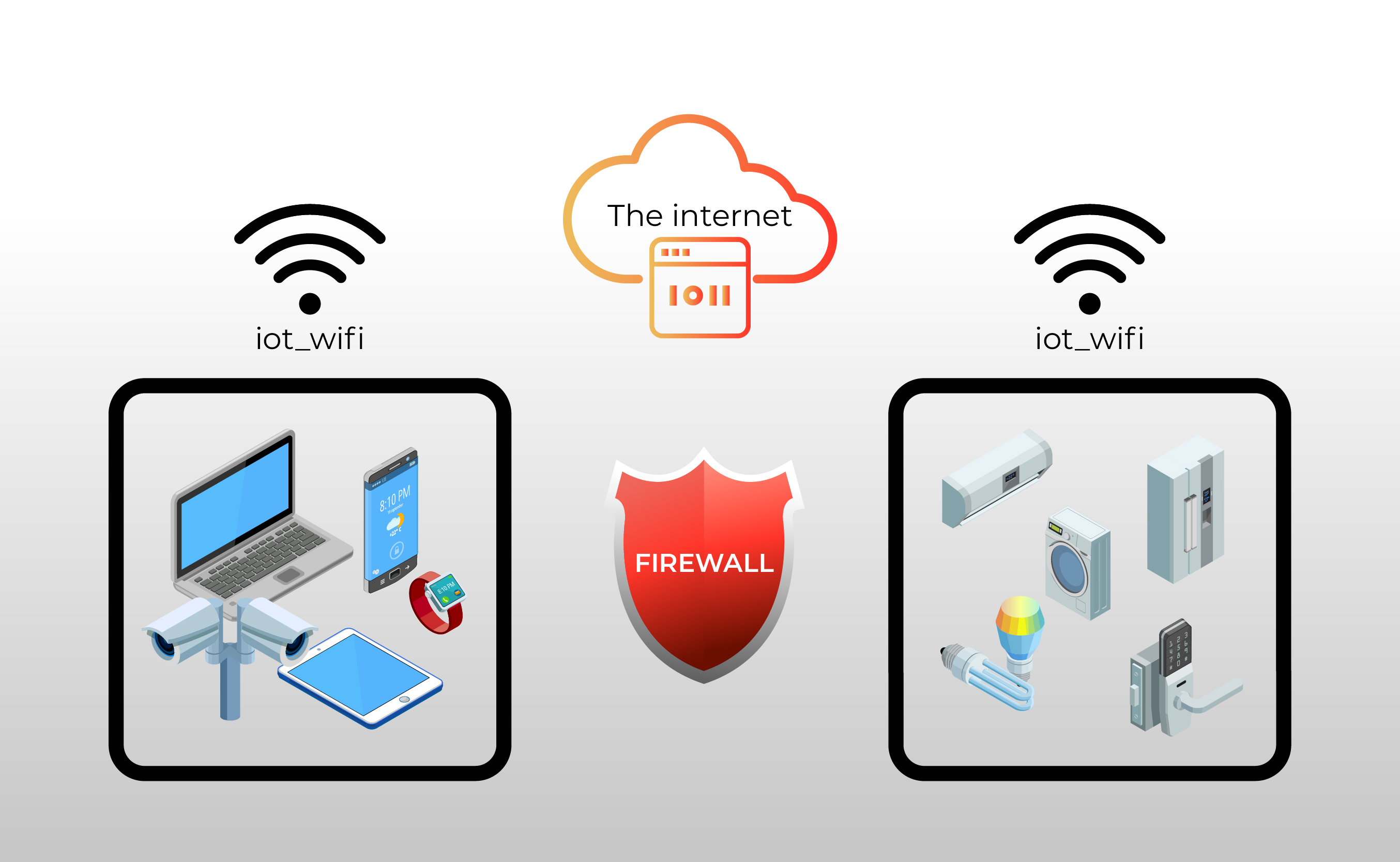
- Segment Networks: Isolate IoT devices on a separate network to limit potential damage from breaches.
- Enable Encryption: Use encryption protocols to protect data transmitted between devices.
- Regularly Update Firmware: Keep IoT device firmware updated to patch security vulnerabilities.
Common IoT Security Threats
IoT devices face a variety of security threats, including:
- DDoS Attacks: Distributed Denial of Service attacks overwhelm devices with traffic, causing them to malfunction.
- Malware Infections: Malicious software can compromise IoT devices and steal data.
- Data Breaches: Unauthorized access to sensitive information stored on IoT devices.
- Physical Tampering: Unauthorized physical access to devices can lead to data theft or system compromise.
Advantages of Using IoT Firewalls
Implementing firewalls for IoT devices offers numerous benefits, including:
- Enhanced Security: Firewalls provide an additional layer of protection against cyber threats.
- Improved Network Performance: By blocking unnecessary traffic, firewalls can optimize network efficiency.
- Compliance with Regulations: Using firewalls helps organizations meet security standards and regulations.
Choosing the Right IoT Firewall
Selecting the appropriate firewall for your IoT devices depends on several factors:
- Network Size: Determine whether a hardware, software, or cloud-based firewall is best suited for your network.
- Security Requirements: Assess the level of protection needed based on the sensitivity of your data.
- Budget Constraints: Consider the cost of implementation and maintenance when choosing a firewall solution.
Future of IoT Firewalls
As IoT continues to evolve, so too will the technology used to secure these devices. Future advancements in firewall technology may include:
- Artificial Intelligence: AI-driven firewalls capable of detecting and responding to threats in real-time.
- Blockchain Integration: Using blockchain to enhance the security and transparency of IoT communications.
- Quantum Computing: Developing firewalls that can withstand the challenges posed by quantum computing advancements.
Kesimpulan
Firewall IoT devices are essential for protecting the growing number of connected devices in our homes and businesses. By understanding the importance of firewalls and implementing best practices for IoT security, you can significantly reduce the risk of cyberattacks. Remember to choose the right firewall solution for your needs and stay informed about emerging trends in IoT security.
We encourage you to take action by reviewing your current security measures and implementing firewalls where necessary. Share this article with others who may benefit from the information, and explore our other resources for further insights into IoT security. Together, we can create a safer, more secure digital environment.