Mastering the use of RemoteIoT behind a firewall on Windows can significantly enhance your ability to manage IoT devices securely while maintaining robust network protection. Whether you're a network administrator, an IT professional, or someone looking to enhance their IoT skills, understanding this process is crucial. This article will provide an in-depth guide on how to configure and use RemoteIoT while ensuring compliance with firewall settings on Windows.
As IoT devices become increasingly prevalent in homes and businesses, managing them remotely has become essential. However, security concerns such as firewalls often create barriers that need to be addressed. In this article, we'll explore the steps required to set up RemoteIoT behind a firewall, ensuring seamless communication while maintaining top-notch security.
This guide will delve into technical details, provide practical tips, and include references to trusted sources to ensure you have all the information needed to implement this solution effectively. Let's dive in!
Table of Contents
- Introduction to RemoteIoT
- Understanding Firewalls
- Overview of RemoteIoT
- Setting Up RemoteIoT Behind Firewall
- Security Best Practices
- Troubleshooting Common Issues
- Improving Performance
- Real-World Use Cases
- Future Trends in RemoteIoT
- Conclusion
Introduction to RemoteIoT
In today's interconnected world, RemoteIoT plays a pivotal role in enabling secure and efficient remote access to IoT devices. The term "RemoteIoT" refers to a suite of tools and technologies designed to facilitate communication between IoT devices and remote users. When working behind a firewall, special considerations must be made to ensure both security and functionality.
Firewalls are essential components of modern network infrastructure, designed to protect networks from unauthorized access. However, they can sometimes block legitimate traffic, including that required for RemoteIoT operations. This article will guide you through configuring RemoteIoT to work seamlessly behind a Windows firewall.
Understanding Firewalls
A firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. Firewalls create a barrier between trusted internal networks and untrusted external networks, such as the internet. They are crucial for protecting sensitive data and preventing unauthorized access.
When using RemoteIoT behind a firewall, understanding how firewalls function is essential. Firewalls can be configured to allow specific types of traffic, which is necessary for RemoteIoT to function properly. Below are some key points to consider:
- Firewalls can be hardware-based or software-based.
- They use rules to determine which traffic is allowed or blocked.
- Windows Firewall is a built-in feature of Windows operating systems, providing basic firewall protection.
Overview of RemoteIoT
RemoteIoT is a powerful tool that allows users to manage IoT devices from a remote location. It provides features such as device monitoring, data collection, and remote control, all while maintaining a secure connection. When used behind a firewall, RemoteIoT requires specific configurations to ensure compatibility and security.
Key features of RemoteIoT include:
- Secure data transfer using encryption protocols.
- Support for multiple IoT protocols, including MQTT and CoAP.
- Integration with cloud platforms for enhanced functionality.
Setting Up RemoteIoT Behind Firewall
Step 1: Prepare Your Environment
Before configuring RemoteIoT behind a firewall, it's essential to prepare your environment. This includes ensuring that all necessary software and hardware components are in place. Follow these steps:
- Ensure your Windows system is up-to-date with the latest security patches.
- Verify that your IoT devices are compatible with RemoteIoT.
- Prepare a list of required ports and protocols for RemoteIoT.
Step 2: Configure Windows Firewall
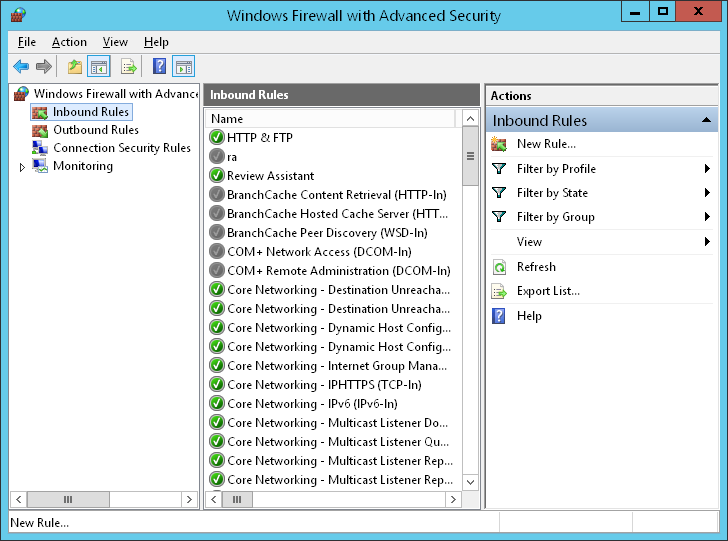
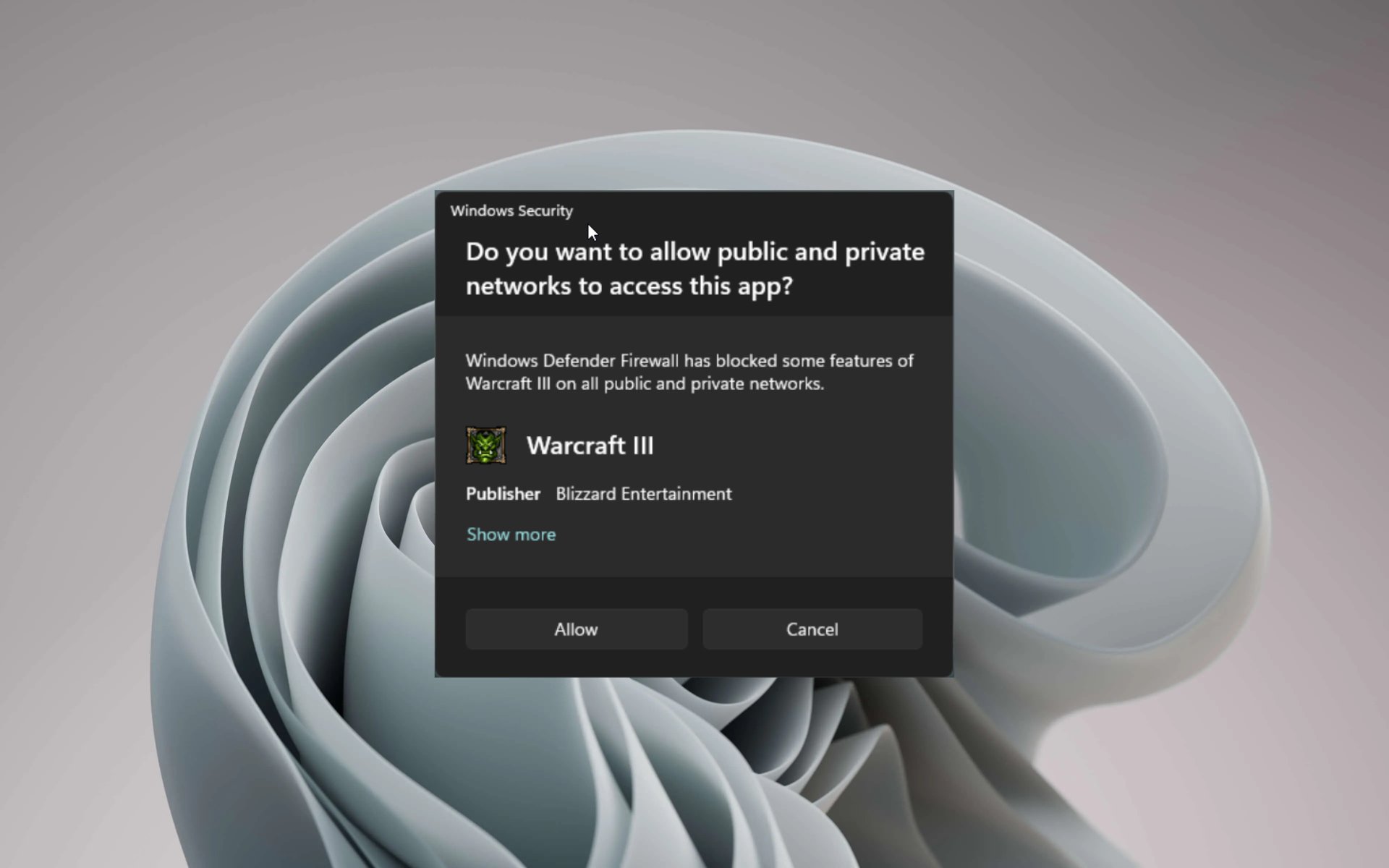
Configuring Windows Firewall is a critical step in setting up RemoteIoT behind a firewall. Follow these steps to ensure proper configuration:
- Open the Windows Firewall settings from the Control Panel.
- Create inbound and outbound rules for the required ports used by RemoteIoT.
- Test the firewall rules to ensure they do not block legitimate traffic.
Step 3: Install RemoteIoT Software
Once the firewall is configured, the next step is to install the RemoteIoT software. Follow these steps:
- Download the latest version of RemoteIoT from the official website.
- Run the installation wizard and follow the on-screen instructions.
- Configure the software to connect to your IoT devices securely.
Security Best Practices
Security is paramount when using RemoteIoT behind a firewall. Here are some best practices to follow:
- Use strong passwords and enable two-factor authentication for added security.
- Regularly update your software and firmware to protect against vulnerabilities.
- Monitor network activity for any suspicious behavior.
Troubleshooting Common Issues
Even with proper configuration, issues can arise when using RemoteIoT behind a firewall. Here are some common problems and their solutions:
- Issue: Connection Refused - Ensure that the required ports are open in the firewall settings.
- Issue: Slow Performance - Optimize network settings and reduce unnecessary traffic.
- Issue: Security Alerts - Review firewall logs and update security rules as needed.
Improving Performance
To enhance the performance of RemoteIoT behind a firewall, consider the following tips:
- Optimize network bandwidth by prioritizing critical traffic.
- Use compression techniques to reduce data transfer size.
- Implement caching mechanisms to minimize redundant data transfers.
Real-World Use Cases
RemoteIoT has numerous applications across various industries. Here are some real-world use cases:
- Smart Home Automation - Manage smart home devices remotely while ensuring security.
- Industrial IoT - Monitor and control industrial equipment from a remote location.
- Healthcare - Enable remote monitoring of medical devices for improved patient care.
Future Trends in RemoteIoT
The future of RemoteIoT is promising, with advancements in technology driving innovation. Some trends to watch include:
- Increased adoption of AI and machine learning for enhanced functionality.
- Integration with 5G networks for faster and more reliable connections.
- Development of new security protocols to address emerging threats.
Conclusion
Using RemoteIoT behind a firewall on Windows requires careful planning and configuration to ensure both security and functionality. By following the steps outlined in this article, you can successfully set up and manage RemoteIoT while maintaining robust network protection. Remember to adhere to security best practices and stay informed about the latest trends in RemoteIoT technology.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT and related technologies. Together, let's build a safer and more connected world!
References:
- Microsoft Docs - Windows Firewall Configuration
- RemoteIoT Official Documentation
- NIST Cybersecurity Framework