RemoteIoT firewall is a critical component for securing IoT devices in remote environments. In today's digital age, where connectivity is essential, understanding how to configure and optimize a firewall for remote IoT setups is more important than ever. This tutorial will provide you with step-by-step guidance to ensure your IoT devices remain secure and protected from potential cyber threats.
With the increasing number of connected devices, securing IoT networks has become a significant challenge for businesses and individuals alike. A well-configured RemoteIoT firewall acts as a shield, preventing unauthorized access and protecting sensitive data. This guide will walk you through the essentials of setting up and maintaining a secure firewall tailored for remote IoT environments.
In this article, we will explore the importance of RemoteIoT firewalls, provide practical tips for configuration, and address common challenges faced during implementation. By the end of this tutorial, you will have a solid understanding of how to safeguard your IoT infrastructure against potential vulnerabilities.
Table of Contents
- Introduction to RemoteIoT Firewalls
- Why RemoteIoT Firewall Matters
- Types of Firewalls for RemoteIoT
- How to Set Up a RemoteIoT Firewall
- Configuration Tips for Optimal Security
- Best Practices for Managing RemoteIoT Firewalls
- Troubleshooting Common Issues
- Enhancing Security with Advanced Features
- Ensuring Scalability for Growing IoT Networks
- Conclusion and Next Steps
Introduction to RemoteIoT Firewalls
A RemoteIoT firewall serves as the first line of defense for IoT devices located in remote areas. These firewalls are specifically designed to handle the unique challenges posed by IoT networks, including limited bandwidth and varying device capabilities. By implementing a robust firewall, you can significantly reduce the risk of unauthorized access and cyberattacks.
What Is a RemoteIoT Firewall?
A RemoteIoT firewall is a security solution tailored for IoT devices that operate in remote environments. It monitors incoming and outgoing network traffic and applies predefined rules to block malicious activities. Unlike traditional firewalls, RemoteIoT firewalls are optimized for the specific needs of IoT devices, ensuring efficient performance even in low-resource conditions.
Key Features of RemoteIoT Firewalls
- Real-time traffic monitoring
- Advanced threat detection
- Customizable rule sets
- Integration with cloud-based management tools
Why RemoteIoT Firewall Matters
In the rapidly evolving landscape of IoT, securing devices in remote locations is paramount. Without proper protection, these devices become vulnerable to attacks such as data breaches, denial-of-service (DoS), and unauthorized access. A RemoteIoT firewall ensures that your network remains secure by filtering out malicious traffic and enforcing strict access controls.
According to a report by Cybersecurity Ventures, the global cost of cybercrime is expected to reach $10.5 trillion annually by 2025. This highlights the critical need for robust security measures, including firewalls, to protect IoT infrastructure.
Types of Firewalls for RemoteIoT
There are several types of firewalls available for securing RemoteIoT networks. Each type offers unique features and benefits, depending on the specific requirements of your setup.
Packet Filtering Firewalls
Packet filtering firewalls analyze individual packets of data and decide whether to allow or block them based on predefined rules. These firewalls are simple and efficient but may lack advanced features required for complex IoT setups.
Stateful Inspection Firewalls
Stateful inspection firewalls track active connections and use this information to make more informed decisions about allowing or blocking traffic. This type of firewall provides better security than packet filtering firewalls and is suitable for most RemoteIoT applications.
Next-Generation Firewalls (NGFW)
NGFWs combine traditional firewall capabilities with advanced features such as intrusion prevention, application awareness, and deep packet inspection. These firewalls are ideal for securing large-scale IoT networks with diverse device types.
How to Set Up a RemoteIoT Firewall
Setting up a RemoteIoT firewall involves several key steps, from selecting the right hardware or software to configuring rules and policies. Below is a step-by-step guide to help you through the process:
Step 1: Choose the Right Firewall Solution
Select a firewall that meets the specific needs of your RemoteIoT network. Consider factors such as scalability, ease of use, and integration capabilities when making your decision.
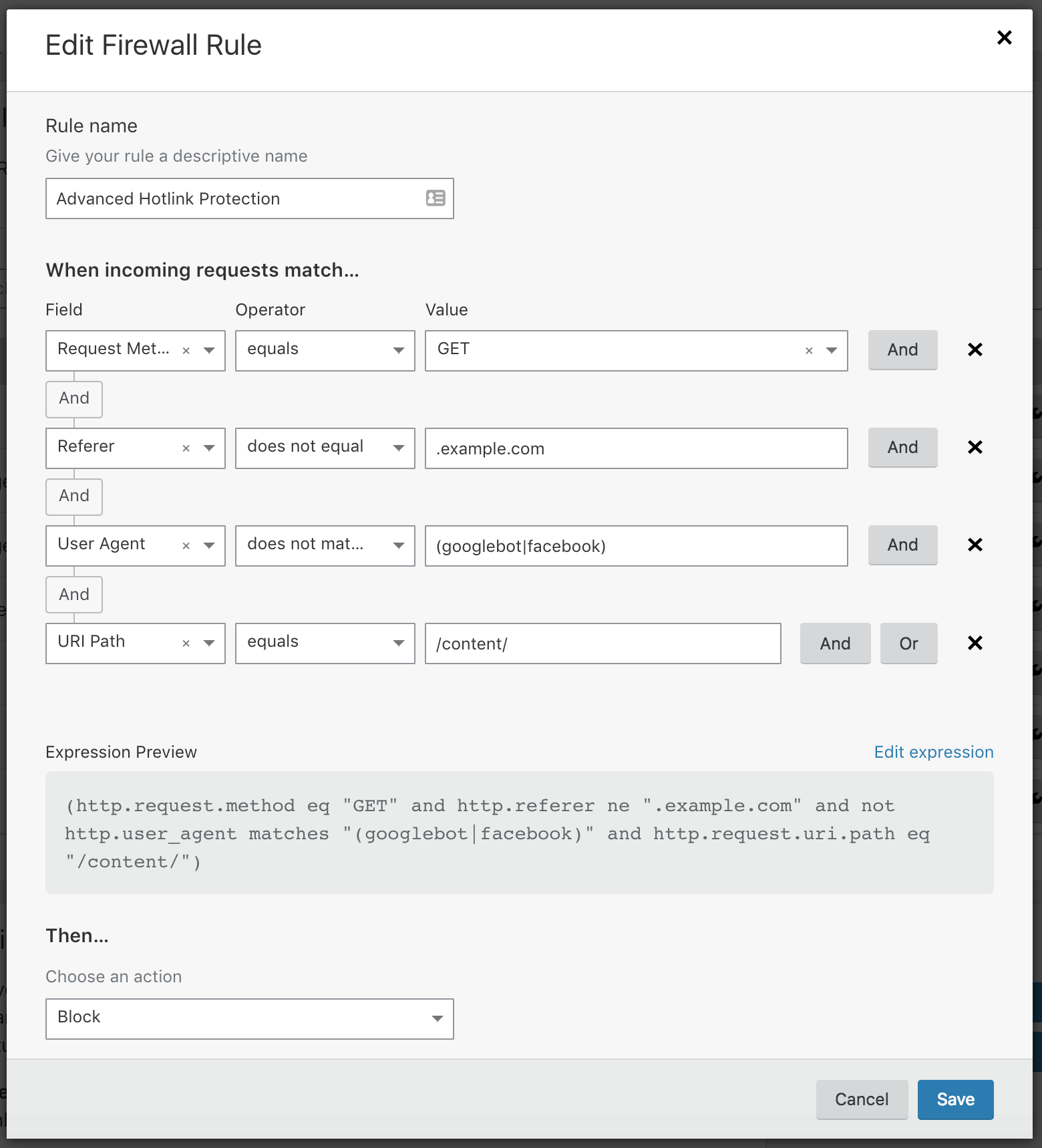
Step 2: Install and Configure the Firewall
Install the chosen firewall solution on your network and configure it according to your security requirements. This may involve setting up access rules, defining traffic filters, and enabling advanced features.
Step 3: Test and Optimize
Once the firewall is installed and configured, test it thoroughly to ensure it functions as expected. Make any necessary adjustments to optimize performance and security.
Configuration Tips for Optimal Security
Proper configuration is essential for maximizing the effectiveness of your RemoteIoT firewall. Below are some tips to help you achieve optimal security:
1. Define Clear Access Rules
Create detailed access rules that specify which devices and users are allowed to access your network. Use IP addresses, MAC addresses, and other identifiers to ensure precise control over network traffic.
2. Enable Logging and Monitoring
Activate logging and monitoring features to track network activity and detect potential threats. Regularly review logs to identify suspicious behavior and take appropriate action.
3. Update Regularly
Keep your firewall software up to date with the latest security patches and updates. This ensures that you are protected against the latest threats and vulnerabilities.
Best Practices for Managing RemoteIoT Firewalls
Managing a RemoteIoT firewall requires ongoing effort and attention to detail. Follow these best practices to maintain a secure and efficient network:
Regular Audits
Conduct regular audits of your firewall configuration to ensure it remains aligned with your security objectives. Identify and address any weaknesses or vulnerabilities that may have arisen since the last audit.
Employee Training
Train employees on the importance of cybersecurity and how to use RemoteIoT firewalls effectively. This helps create a culture of security awareness within your organization.
Backup and Recovery Plans
Develop comprehensive backup and recovery plans to ensure your network can quickly recover from any disruptions or attacks. Regularly test these plans to verify their effectiveness.
Troubleshooting Common Issues
Even with the best planning and implementation, issues can arise when managing a RemoteIoT firewall. Below are some common problems and their solutions:
Blocked Legitimate Traffic
If legitimate traffic is being blocked by your firewall, review your access rules and adjust them as necessary. Ensure that all required devices and users are correctly configured in your rule set.
Performance Degradation
Performance issues can occur if your firewall is overloaded with traffic or lacks sufficient resources. Consider upgrading your hardware or optimizing your configuration to improve performance.
Enhancing Security with Advanced Features
Modern RemoteIoT firewalls offer a range of advanced features to enhance network security. These include:
Intrusion Detection and Prevention
Implement intrusion detection and prevention systems (IDPS) to identify and block potential attacks before they can cause damage.
Application Control
Use application control features to regulate which applications can access your network, reducing the risk of unauthorized access and data breaches.
Ensuring Scalability for Growing IoT Networks
As your IoT network grows, it is essential to ensure that your RemoteIoT firewall can scale to meet increasing demands. Consider the following strategies to maintain scalability:
Cloud-Based Solutions
Adopt cloud-based firewall solutions that can dynamically scale to accommodate changing network requirements.
Modular Architecture
Design your network with a modular architecture that allows for easy expansion and integration of new devices and services.
Conclusion and Next Steps
In conclusion, a well-configured RemoteIoT firewall is vital for securing your IoT devices in remote environments. By following the guidance provided in this tutorial, you can ensure your network remains protected against potential threats and vulnerabilities.
We encourage you to take action by implementing the tips and best practices outlined in this article. Don't forget to share your thoughts and experiences in the comments section below. For more insights into IoT security, explore our other articles and resources.
References:
![[PDF] Firewall free tutorial for Beginners](https://www.computer-pdf.com/documents/covers/0175-firewall-tutorial.pdf.png)