As the Internet of Things (IoT) continues to expand, controlling IoT devices behind a firewall has become a critical aspect of modern networking and security. Whether you're managing smart home appliances, industrial sensors, or enterprise-level devices, understanding how to control IoT devices securely is essential. In this article, we will explore the best practices, tools, and techniques for ensuring seamless communication while maintaining robust security.
IoT devices are becoming increasingly common in both personal and professional environments. However, their integration into networks protected by firewalls requires careful consideration. This guide aims to provide you with the knowledge and tools necessary to effectively manage and control IoT devices while maintaining network integrity.
By the end of this article, you will gain insights into the challenges, solutions, and strategies for controlling IoT devices behind firewalls. Let's dive in!
Table of Contents
- Introduction to IoT Devices
- Understanding Firewall Basics
- Challenges in Controlling IoT Devices Behind Firewalls
- Solutions for Managing IoT Devices
- Tools for IoT Device Management
- Enhancing Security for IoT Devices
- Network Configuration for IoT Devices
- Best Practices for IoT Device Control
- Future Trends in IoT and Firewalls
- Conclusion
Introduction to IoT Devices
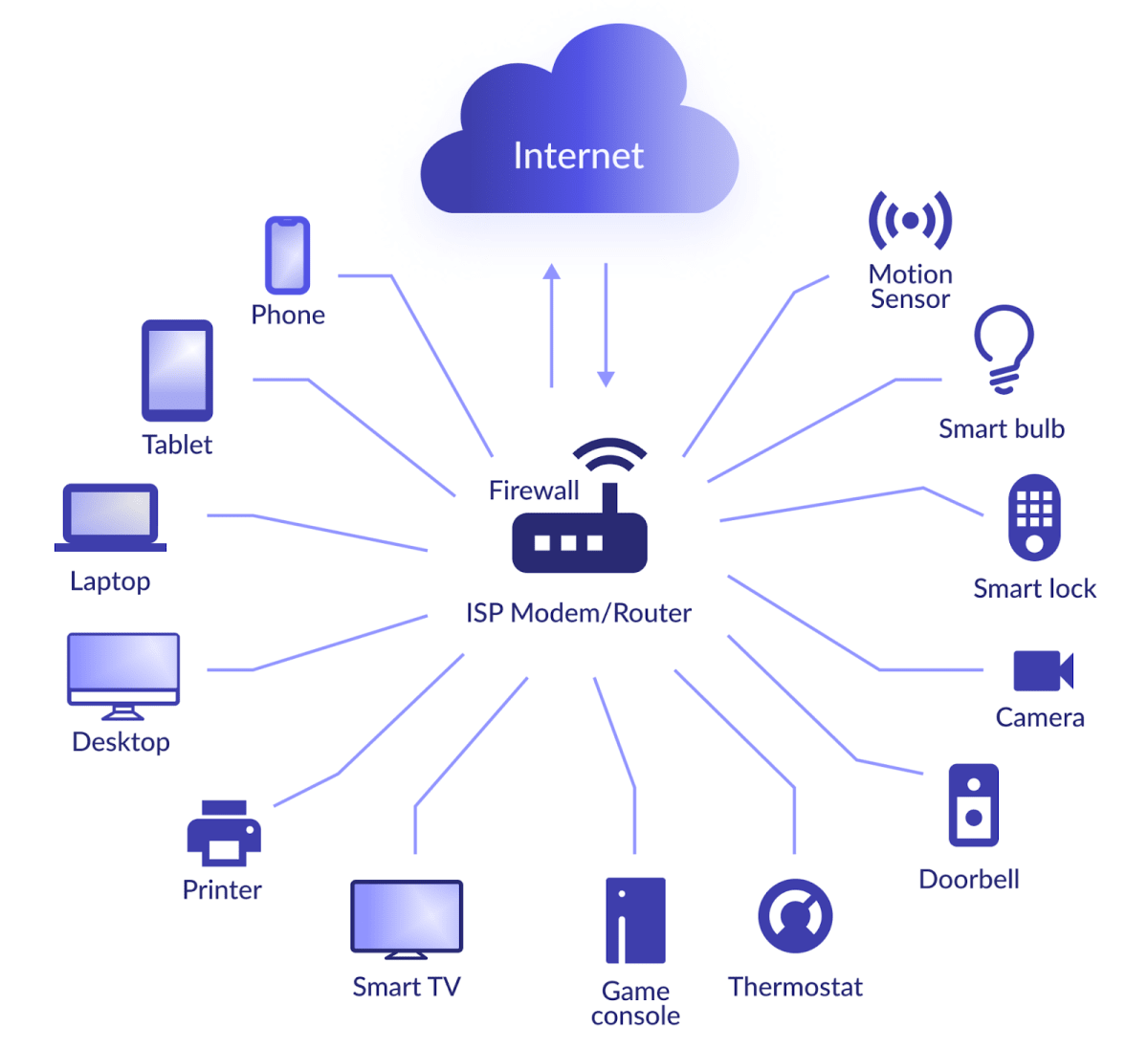
IoT devices refer to interconnected gadgets and appliances that communicate and share data via the internet. These devices range from simple home automation tools like smart bulbs to complex industrial sensors monitoring critical infrastructure. The proliferation of IoT devices has transformed various sectors, including healthcare, manufacturing, and transportation.
However, the integration of IoT devices into networks often poses challenges, especially when firewalls are involved. Firewalls are designed to protect networks by filtering incoming and outgoing traffic based on predetermined security rules. Balancing security with functionality is crucial when controlling IoT devices behind firewalls.
Key Features of IoT Devices
- Interconnectivity with other devices
- Real-time data transmission
- Automation capabilities
- Remote accessibility
Understanding Firewall Basics
A firewall is a network security system that monitors and controls incoming and outgoing network traffic. It acts as a barrier between trusted internal networks and untrusted external networks, such as the internet. Firewalls use a set of rules to determine which traffic is allowed or blocked, ensuring the security and integrity of the network.
When IoT devices are connected to a network protected by a firewall, certain challenges arise. These challenges include managing data flow, ensuring device compatibility, and maintaining security protocols.
Types of Firewalls
- Packet-filtering firewalls
- Stateful inspection firewalls
- Application-level gateways
- Next-generation firewalls
Challenges in Controlling IoT Devices Behind Firewalls
Controlling IoT devices behind firewalls presents several challenges. One of the primary issues is ensuring that devices can communicate effectively without compromising network security. Additionally, IoT devices often use non-standard protocols, which can complicate firewall configurations.
Another challenge is managing the sheer volume of data generated by IoT devices. Firewalls must be able to handle this data efficiently while maintaining security. Furthermore, the lack of standardization in IoT protocols can lead to compatibility issues with firewalls.
Common Challenges
- Data flow management
- Device compatibility
- Security protocol enforcement
- Scalability
Solutions for Managing IoT Devices
To address the challenges of controlling IoT devices behind firewalls, several solutions can be implemented. These solutions focus on enhancing security, improving device compatibility, and optimizing network performance.
One effective solution is to use application-level gateways, which provide detailed inspection of traffic at the application layer. This allows for more granular control over IoT device communications. Additionally, implementing next-generation firewalls can offer advanced threat detection and protection capabilities.
Implementing Solutions
- Deploy application-level gateways
- Utilize next-generation firewalls
- Configure firewall rules for IoT devices
- Monitor and analyze network traffic
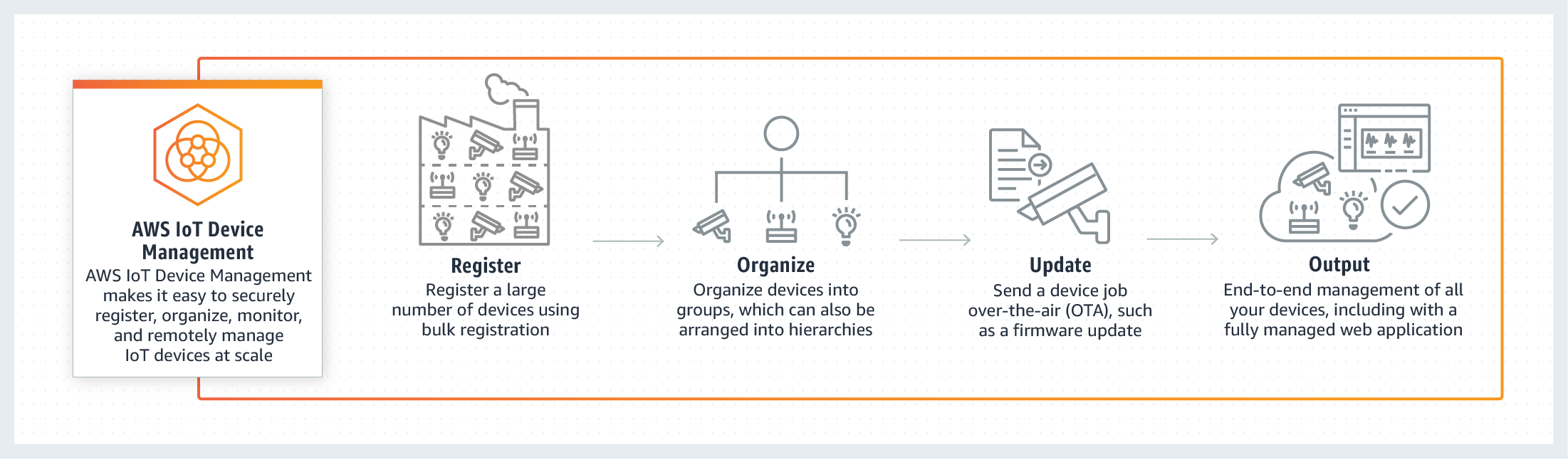
Tools for IoT Device Management
Several tools are available to assist in managing IoT devices behind firewalls. These tools provide features such as device discovery, traffic monitoring, and security analysis. By leveraging these tools, network administrators can gain better visibility and control over their IoT devices.
Some popular tools for IoT device management include:
Popular Tools
- Wireshark
- Snort
- OpenWrt
- IoT Inspector
Enhancing Security for IoT Devices
Security is a top priority when controlling IoT devices behind firewalls. Implementing robust security measures is essential to protect sensitive data and prevent unauthorized access. Some best practices for enhancing security include regular firmware updates, strong authentication mechanisms, and encryption of data transmissions.
Furthermore, network segmentation can be used to isolate IoT devices from other network components, reducing the risk of a security breach. Regular security audits and vulnerability assessments are also recommended to ensure ongoing protection.
Security Best Practices
- Regular firmware updates
- Strong authentication mechanisms
- Data encryption
- Network segmentation
Network Configuration for IoT Devices
Proper network configuration is crucial for controlling IoT devices behind firewalls. This involves setting up firewall rules, configuring network settings, and ensuring compatibility with IoT protocols. By optimizing network configurations, administrators can improve device performance and enhance security.
One effective strategy is to use virtual local area networks (VLANs) to segment IoT devices from other network components. This allows for more granular control over device communications and reduces the risk of unauthorized access.
Configuration Tips
- Set up firewall rules for IoT devices
- Use VLANs for network segmentation
- Configure network settings for optimal performance
- Ensure compatibility with IoT protocols
Best Practices for IoT Device Control
To effectively control IoT devices behind firewalls, it is important to follow best practices. These practices include regular maintenance, monitoring, and updates to ensure optimal performance and security. Additionally, educating users about IoT device security can help prevent common vulnerabilities.
Regularly reviewing and updating firewall rules is another best practice. This ensures that the firewall remains aligned with the evolving needs of the network and its IoT devices. Continuous monitoring of network traffic can also help identify and address potential security threats.
Best Practices Checklist
- Regular maintenance and updates
- Continuous monitoring
- User education
- Regular review of firewall rules
Future Trends in IoT and Firewalls
The future of IoT and firewalls is shaped by emerging technologies and trends. As IoT devices continue to evolve, so too will the tools and techniques used to manage them. One trend is the increasing use of artificial intelligence (AI) and machine learning (ML) in firewall technologies, enabling more intelligent and adaptive security measures.
Another trend is the development of standardized protocols for IoT devices, which will improve compatibility and simplify firewall configurations. Additionally, the adoption of edge computing can enhance the performance and security of IoT devices by processing data closer to the source.
Emerging Trends
- AI and ML in firewalls
- Standardized IoT protocols
- Edge computing
- 5G networks
Conclusion
Controlling IoT devices behind firewalls requires a comprehensive approach that balances security with functionality. By understanding the challenges, implementing effective solutions, and following best practices, network administrators can successfully manage IoT devices while maintaining network integrity.
We encourage you to share your thoughts and experiences in the comments below. Additionally, explore our other articles for more insights into IoT and network security. Together, we can build a safer and more connected future.