In today's interconnected world, accessing remote IoT devices has become an essential skill for tech enthusiasts, professionals, and businesses alike. The Internet of Things (IoT) has revolutionized the way we interact with devices, enabling seamless connectivity across vast distances. Understanding how to securely and effectively access remote IoT devices is crucial for optimizing performance, monitoring systems, and ensuring data integrity.
As more devices become connected to the internet, the demand for remote access capabilities continues to grow. This tutorial aims to provide a step-by-step guide on how to access remote IoT devices, ensuring that users can manage their devices efficiently and securely. Whether you're a beginner or an experienced professional, this guide will equip you with the knowledge and tools necessary to navigate the complexities of remote IoT device management.
By the end of this tutorial, you'll gain insights into the best practices for accessing remote IoT devices, including security measures, troubleshooting techniques, and the latest technologies available. Let's dive into the world of IoT and explore how you can harness its potential to enhance your operations.
Table of Contents
- Introduction to Remote IoT Devices
- Why Access Remote IoT Devices?
- Tools for Remote IoT Device Access
- Security Considerations
- Step-by-Step Tutorial
- Common Issues and Solutions
- Best Practices
- Future of Remote IoT Access
- Real-World Applications
- Conclusion
Introduction to Remote IoT Devices
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity capabilities that enable them to exchange data. Remote IoT devices are those that can be accessed and managed from a distance, often through cloud-based platforms or specialized software. These devices range from smart home appliances to industrial machinery, all designed to enhance efficiency and convenience.
Accessing remote IoT devices allows users to monitor and control their operations without being physically present. This capability is particularly beneficial in industries such as agriculture, healthcare, and manufacturing, where real-time data analysis and device management are critical.
Benefits of Remote IoT Device Access
- Increased operational efficiency
- Real-time data monitoring
- Reduced downtime and maintenance costs
- Enhanced scalability and flexibility
Why Access Remote IoT Devices?
Accessing remote IoT devices offers numerous advantages, especially in today's fast-paced world where time and resources are limited. By leveraging remote access, businesses can streamline their operations, reduce costs, and improve decision-making processes.
Key Reasons for Remote Access
- Cost Efficiency: Eliminate the need for on-site visits, reducing travel expenses and labor costs.
- Real-Time Monitoring: Gain instant access to device data, enabling proactive maintenance and troubleshooting.
- Scalability: Easily manage multiple devices across different locations from a centralized platform.
According to a report by Statista, the global IoT market is expected to reach $1.5 trillion by 2030, highlighting the growing importance of remote IoT device access in various industries.
Tools for Remote IoT Device Access
Several tools and platforms are available to facilitate the access and management of remote IoT devices. Choosing the right tool depends on the specific needs of your project and the type of devices you're working with.
Popular Tools for Remote IoT Access
- MQTT (Message Queuing Telemetry Transport): A lightweight protocol ideal for low-bandwidth environments.
- Amazon Web Services (AWS) IoT: A cloud-based platform offering robust features for IoT device management.
- Microsoft Azure IoT Hub: A comprehensive solution for connecting, monitoring, and managing IoT devices at scale.
These tools provide secure and reliable ways to access remote IoT devices, ensuring seamless communication and data exchange.
Security Considerations
Security is a critical aspect of accessing remote IoT devices. With the increasing number of cyber threats, it's essential to implement robust security measures to protect your devices and data.
Best Security Practices
- Encryption: Use end-to-end encryption to secure data transmission between devices and servers.
- Authentication: Implement strong authentication mechanisms, such as multi-factor authentication, to ensure only authorized users can access the devices.
- Regular Updates: Keep your devices and software up to date with the latest security patches and firmware updates.
A study by IBM found that 60% of data breaches are caused by compromised credentials, emphasizing the importance of secure authentication practices.
Step-by-Step Tutorial
Here's a detailed guide on how to access remote IoT devices securely and efficiently:
Step 1: Set Up Your IoT Device
Begin by configuring your IoT device according to the manufacturer's instructions. Ensure that the device is connected to the internet and properly set up for remote access.
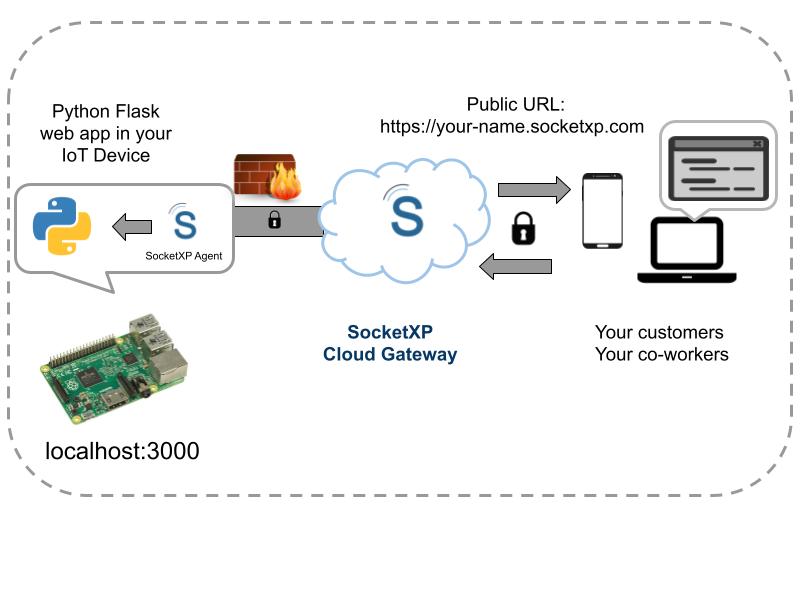
Step 2: Choose a Remote Access Platform
Select a reliable platform that supports remote IoT device access. Options such as AWS IoT, Microsoft Azure IoT Hub, or MQTT can be considered based on your specific requirements.
Step 3: Secure Your Connection
Implement encryption and authentication protocols to secure your connection. Use SSL/TLS for data encryption and configure firewalls to protect against unauthorized access.
Step 4: Access Your Device Remotely
Once your device is configured and secured, you can access it remotely through the chosen platform. Monitor its performance, update settings, and troubleshoot issues as needed.
Common Issues and Solutions
While accessing remote IoT devices, you may encounter certain challenges. Here are some common issues and their solutions:
Issue 1: Connectivity Problems
Solution: Check the device's network settings and ensure a stable internet connection. Restart the device if necessary.
Issue 2: Authentication Failures
Solution: Verify your login credentials and ensure that multi-factor authentication is properly configured.
Issue 3: Data Security Breaches
Solution: Regularly update your security protocols and monitor for any suspicious activity.
Best Practices
Adopting best practices for remote IoT device access can significantly enhance your experience and ensure optimal performance. Here are some tips to consider:
- Regularly back up your device data to prevent data loss.
- Document all configurations and settings for easy reference.
- Limit access to authorized personnel only to minimize security risks.
Future of Remote IoT Access
The future of remote IoT device access looks promising, with advancements in technology driving innovation in this field. Emerging trends such as edge computing, artificial intelligence, and 5G networks are expected to transform the way we interact with IoT devices.
Predicted Trends
- Edge Computing: Processing data closer to the source to reduce latency and improve efficiency.
- AI Integration: Leveraging artificial intelligence for predictive maintenance and automated decision-making.
- 5G Connectivity: Enabling faster and more reliable communication between devices.
Real-World Applications
Remote IoT device access has already made a significant impact in various industries. Here are some real-world applications:
Healthcare
Remote monitoring of medical devices allows healthcare providers to track patient health in real-time, improving diagnostic accuracy and treatment outcomes.
Manufacturing
In the manufacturing sector, remote access enables predictive maintenance, reducing downtime and optimizing production processes.
Agriculture
Farmers use remote IoT devices to monitor soil conditions, weather patterns, and crop health, leading to more sustainable and efficient farming practices.
Conclusion
Accessing remote IoT devices has become an indispensable skill in today's digital age. This tutorial has provided a comprehensive guide on how to securely and effectively manage remote IoT devices, covering everything from setup to troubleshooting and best practices.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore our other articles for more insights into the world of IoT and technology. Together, let's embrace the future of connectivity and innovation!
![How to Access IoT Devices Remotely with SSH [6 Easy Steps] cloud](https://cloud.lavainfo.my.id/wp-content/uploads/2024/10/Access-IoT-Devices-Remotely-Using-SSH.webp.webp)