IoT SSH over internet example is becoming increasingly relevant as more devices connect to the global network. With the rise of smart devices, remote management and secure access have become critical for both individuals and organizations. This guide explores how to implement secure shell (SSH) connections for IoT devices over the internet, ensuring robust security and reliability.
As the Internet of Things (IoT) continues to expand, managing devices remotely has become essential. Whether for home automation, industrial applications, or smart city infrastructure, secure remote access is crucial. SSH provides a reliable and encrypted method to manage IoT devices from anywhere in the world.
This article delves into the technical aspects of setting up SSH for IoT devices, including best practices, security considerations, and real-world examples. By the end of this guide, you'll have a comprehensive understanding of how to configure and manage IoT SSH over the internet safely and effectively.
Table of Contents
- Introduction to IoT SSH
- Why Use SSH for IoT?
- Setting Up SSH on IoT Devices
- Securing SSH Connections
- Real-World IoT SSH Examples
- Common SSH Issues and Troubleshooting
- Best Practices for IoT SSH
- IoT SSH Security Trends
- Tools for Managing IoT SSH
- Conclusion and Next Steps
Introduction to IoT SSH
SSH, or Secure Shell, is a protocol that facilitates secure communication between devices over an unsecured network. In the context of IoT, SSH enables administrators to remotely access and manage IoT devices securely. This is particularly important as IoT devices often operate in environments where physical access is limited or impossible.
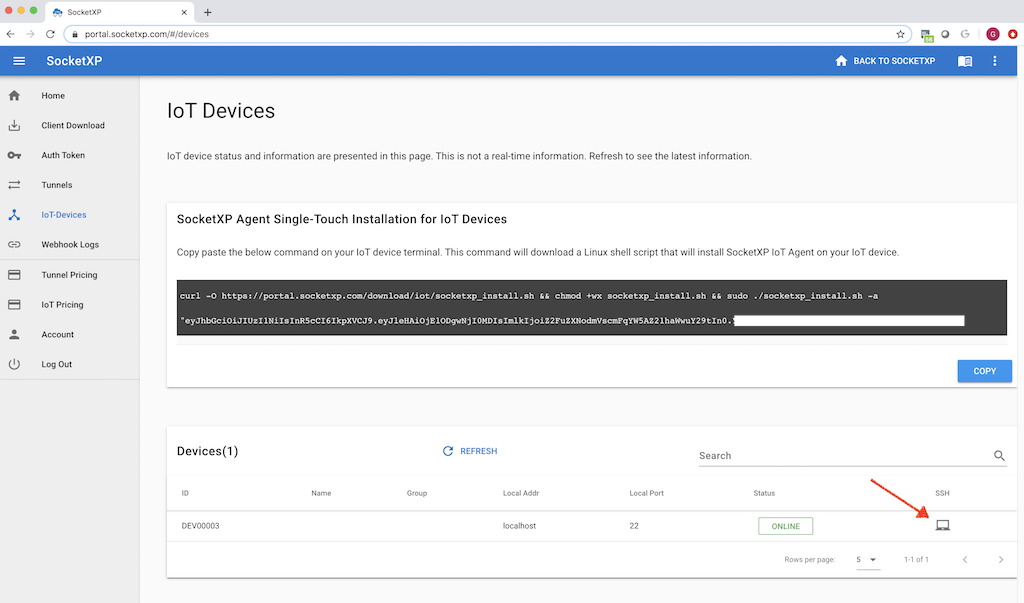
IoT SSH over internet example demonstrates how secure communication can be established between a local machine and a remote IoT device. By leveraging SSH, users can execute commands, transfer files, and monitor device performance without compromising security.
The importance of SSH in IoT cannot be overstated. With the proliferation of IoT devices, ensuring secure communication is paramount. SSH provides encryption, authentication, and integrity checks, making it an ideal choice for remote access in IoT applications.
Why Use SSH for IoT?
Using SSH for IoT devices offers several advantages:
- Security: SSH encrypts all data transmitted between devices, protecting sensitive information from unauthorized access.
- Reliability: SSH ensures that communication remains uninterrupted, even in unstable network conditions.
- Flexibility: SSH supports various commands and protocols, making it versatile for different IoT applications.
- Authentication: SSH provides robust authentication mechanisms, ensuring only authorized users can access IoT devices.
These benefits make SSH an indispensable tool for managing IoT devices over the internet. As more devices connect to the internet, the need for secure remote access solutions like SSH continues to grow.
Setting Up SSH on IoT Devices
Step 1: Enable SSH
The first step in setting up SSH for IoT devices is enabling the SSH service. Most modern IoT devices come with SSH pre-installed, but it may need to be activated. For example, on a Raspberry Pi, you can enable SSH by:
- Accessing the device's configuration settings.
- Locating the SSH option and enabling it.
- Rebooting the device to apply changes.
Once SSH is enabled, you can connect to the device using an SSH client like PuTTY or OpenSSH.
Step 2: Configure Firewall
Configuring the firewall is essential to ensure only authorized connections can access the IoT device. By default, SSH operates on port 22. You can modify this port to enhance security and reduce the risk of brute-force attacks.
To configure the firewall:
- Identify the IP address of the IoT device.
- Set up rules to allow incoming connections on the specified SSH port.
- Block all other unnecessary ports to minimize vulnerabilities.
These steps help secure the IoT device while maintaining accessibility for authorized users.
Securing SSH Connections
While SSH is inherently secure, additional measures can further enhance its protection. Here are some best practices for securing SSH connections:
- Use Strong Passwords: Ensure all user accounts have strong, unique passwords.
- Enable Key-Based Authentication: Replace password-based authentication with SSH keys for added security.
- Disable Root Login: Restrict direct root access to prevent unauthorized administrative control.
- Monitor Logs: Regularly review SSH logs to detect and respond to suspicious activities.
Implementing these practices significantly reduces the risk of unauthorized access and ensures the integrity of IoT SSH connections.
Real-World IoT SSH Examples
Several industries utilize IoT SSH over the internet for various applications. Below are some real-world examples:
- Smart Agriculture: Farmers use IoT devices to monitor soil moisture and temperature. SSH enables remote configuration and troubleshooting of these devices.
- Industrial Automation: Manufacturers employ IoT sensors to track production line performance. SSH provides secure access for maintenance and updates.
- Smart Homes: Homeowners manage smart thermostats and security systems using SSH, ensuring privacy and convenience.
These examples highlight the versatility and importance of SSH in IoT applications across different sectors.
Common SSH Issues and Troubleshooting
Despite its reliability, SSH can encounter issues. Common problems include:
- Connection Refused: Ensure the SSH service is running and the correct port is open.
- Authentication Failure: Verify the username, password, or SSH key being used.
- Timeout Errors: Check network connectivity and firewall settings.
By systematically addressing these issues, you can resolve most SSH-related problems and maintain seamless connectivity.
Best Practices for IoT SSH
Adopting best practices is crucial for effective IoT SSH management. Consider the following tips:
- Regular Updates: Keep the SSH software and firmware of IoT devices up to date.
- Network Segmentation: Isolate IoT devices on a separate network to enhance security.
- Access Control: Limit SSH access to trusted IP addresses or networks.
- Documentation: Maintain detailed records of SSH configurations and changes.
These practices contribute to a more secure and manageable IoT SSH environment.
IoT SSH Security Trends
The landscape of IoT SSH security is continually evolving. Emerging trends include:
- Quantum-Resistant Cryptography: Developing encryption methods resistant to quantum computing attacks.
- Zero-Trust Architecture: Implementing strict verification processes for every connection attempt.
- AI-Driven Monitoring: Leveraging artificial intelligence to detect and respond to potential threats in real-time.
Staying informed about these trends helps organizations prepare for future challenges in IoT SSH security.
Tools for Managing IoT SSH
Several tools simplify the management of IoT SSH connections:
- OpenSSH: A widely-used open-source SSH implementation offering robust features.
- Bitvise SSH Client: A powerful tool for Windows users, providing advanced security options.
- SecureCRT: A comprehensive SSH client supporting multiple protocols and customization options.
These tools enhance productivity and streamline the management of IoT SSH connections.
Conclusion and Next Steps
In conclusion, IoT SSH over internet example demonstrates the significance of secure remote access in modern IoT applications. By following the guidelines and best practices outlined in this article, you can effectively configure and manage SSH connections for your IoT devices.
We encourage readers to:
- Experiment with SSH configurations on their IoT devices.
- Explore additional security measures to further protect their networks.
- Share their experiences and insights in the comments section below.
Thank you for reading! For more informative content on IoT and related technologies, explore our other articles and resources.
References:
- OpenSSH Documentation: https://www.openssh.com/
- IoT Security Best Practices: https://www.nist.gov/
- Quantum Computing and Cryptography: https://www.ibm.com/