Remote IoT platforms powered by SSH offer a secure and efficient way to manage Internet of Things devices from anywhere in the world. As the demand for connected devices grows, so does the need for robust security protocols. SSH (Secure Shell) ensures encrypted communication, making it an ideal choice for IoT applications. This guide will provide you with comprehensive insights into how remote IoT platforms leverage SSH to enhance security, scalability, and usability.
In today's interconnected world, IoT devices are transforming industries and daily life. From smart homes to industrial automation, these devices rely on secure communication channels to function effectively. The integration of SSH into remote IoT platforms addresses critical security concerns, protecting sensitive data and ensuring uninterrupted operations.
This article aims to demystify the concept of remote IoT platforms using SSH. By exploring various aspects such as setup, security protocols, and real-world applications, you'll gain a deeper understanding of how this technology can benefit your organization or personal projects. Let's dive in!
Table of Contents
- Introduction to Remote IoT Platforms
- Understanding SSH: A Brief Overview
- How SSH Integrates with IoT Platforms
- Key Benefits of Using SSH in Remote IoT Platforms
- Enhancing Security with SSH
- Setting Up a Remote IoT Platform with SSH
- Real-World Applications of Remote IoT Platforms
- Common Challenges and Solutions
- The Future of Remote IoT Platforms
- Conclusion
Introduction to Remote IoT Platforms
Remote IoT platforms are cloud-based systems designed to manage and monitor IoT devices from distant locations. These platforms enable users to access device data, configure settings, and troubleshoot issues without physical presence. With the increasing number of connected devices, the need for scalable and secure remote management solutions has never been more critical.
Why Use Remote IoT Platforms?
Remote IoT platforms offer several advantages, including:
- Centralized control over multiple devices.
- Real-time data monitoring and analysis.
- Reduced operational costs by eliminating the need for on-site maintenance.
- Improved scalability, allowing businesses to expand their IoT networks effortlessly.
By integrating SSH into these platforms, organizations can enhance security, ensuring that sensitive data remains protected during transmission.
Understanding SSH: A Brief Overview
SSH, or Secure Shell, is a network protocol designed to secure communications between devices over an unsecured network. It provides encryption for data transfer, ensuring that information remains private and tamper-proof. SSH is widely used in remote server management, file transfers, and secure command execution.
Key Features of SSH
- Data encryption using strong cryptographic algorithms.
- Authentication mechanisms to verify user identity.
- Support for secure file transfers via SFTP (SSH File Transfer Protocol).
SSH's robust security features make it an ideal choice for remote IoT platforms, where securing data communication is paramount.
How SSH Integrates with IoT Platforms
Integrating SSH into IoT platforms involves configuring devices to communicate securely using the protocol. This process typically includes setting up SSH servers on IoT devices and establishing secure connections from remote clients. By leveraging SSH, IoT platforms can ensure that all data exchanges are encrypted and authenticated.
Steps to Integrate SSH
To integrate SSH into an IoT platform, follow these steps:
- Install an SSH server on each IoT device.
- Configure firewall settings to allow SSH traffic.
- Set up user authentication using SSH keys or passwords.
- Test the connection to ensure secure communication.
This integration process ensures that all interactions with IoT devices are secure and reliable.
Key Benefits of Using SSH in Remote IoT Platforms
Using SSH in remote IoT platforms offers numerous benefits that enhance both security and usability. These advantages include:
- Enhanced Security: SSH encrypts all data transmissions, protecting sensitive information from interception.
- Reliability: The protocol ensures stable connections even in challenging network conditions.
- Scalability: SSH can handle large-scale IoT deployments without compromising performance.
- Compatibility: The protocol works seamlessly with a wide range of devices and operating systems.
These benefits make SSH an indispensable tool for modern remote IoT platforms.
Enhancing Security with SSH
Security is a top priority in IoT applications, and SSH plays a crucial role in safeguarding these systems. By encrypting data transmissions and authenticating users, SSH minimizes the risk of unauthorized access and data breaches.
Best Practices for SSH Security
To maximize security when using SSH in remote IoT platforms, consider the following best practices:
- Use SSH keys instead of passwords for authentication.
- Disable root login to prevent unauthorized access.
- Regularly update SSH software to patch vulnerabilities.
- Monitor connection logs for suspicious activities.
Implementing these practices ensures that your IoT platform remains secure against potential threats.
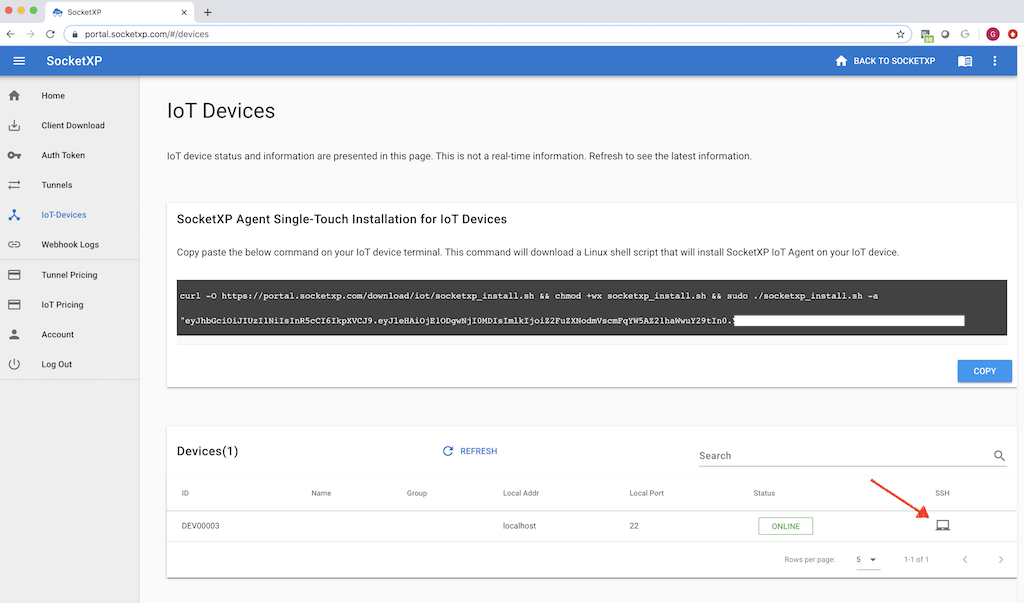
Setting Up a Remote IoT Platform with SSH
Setting up a remote IoT platform with SSH involves several key steps. This section will guide you through the process, ensuring a smooth and secure configuration.
Step-by-Step Guide
- Install the IoT Platform: Choose a reliable platform that supports SSH integration, such as AWS IoT or Microsoft Azure IoT.
- Configure Devices: Set up SSH servers on each IoT device, ensuring they are properly configured for secure communication.
- Secure Connections: Implement SSH keys for authentication and test connections to verify secure communication.
- Monitor Performance: Use monitoring tools to track device performance and address any issues promptly.
This setup process ensures that your remote IoT platform is both secure and functional.
Real-World Applications of Remote IoT Platforms
Remote IoT platforms powered by SSH have diverse applications across various industries. Some notable examples include:
- Smart Homes: Remote control of lighting, climate control, and security systems.
- Industrial Automation: Monitoring and managing machinery in manufacturing facilities.
- Agriculture: Real-time monitoring of soil moisture, weather conditions, and crop health.
- Healthcare: Remote patient monitoring and medical device management.
These applications demonstrate the versatility and potential of remote IoT platforms in transforming industries.
Common Challenges and Solutions
While remote IoT platforms offer numerous benefits, they also present certain challenges. Some common issues include:
- Network Latency: Delayed communication between devices and platforms.
- Device Compatibility: Ensuring all devices support SSH integration.
- Security Threats: Protecting against unauthorized access and data breaches.
To address these challenges, organizations should implement robust security measures, optimize network configurations, and choose compatible devices.
The Future of Remote IoT Platforms
The future of remote IoT platforms looks promising, with advancements in technology driving innovation in this field. Emerging trends such as edge computing, artificial intelligence, and 5G connectivity are set to enhance the capabilities of these platforms, enabling more sophisticated applications and improved performance.
Emerging Trends
- Edge computing for faster data processing and reduced latency.
- AI-driven analytics for predictive maintenance and optimized operations.
- 5G networks for enhanced connectivity and bandwidth.
These advancements will further solidify the role of remote IoT platforms in shaping the future of connected technologies.
Conclusion
Remote IoT platforms powered by SSH offer a secure and efficient solution for managing IoT devices from anywhere in the world. By integrating SSH into these platforms, organizations can enhance security, scalability, and usability, enabling them to unlock the full potential of IoT technology.
We encourage you to explore the possibilities of remote IoT platforms and consider implementing SSH for secure communication. Share your thoughts and experiences in the comments below, and don't forget to explore other articles on our site for more insightful content.
References:
- IEEE - "Secure Communication Protocols for IoT Devices"
- MIT Technology Review - "The Future of IoT"
- OWASP - "IoT Security Guidelines"