In today's interconnected world, securely connect remote IoT P2P free has become a necessity for developers and enthusiasts alike. The rise of Internet of Things (IoT) devices demands robust security measures to ensure seamless communication. Among the popular platforms, Raspberry Pi stands out as a versatile tool for implementing secure IoT solutions. This article delves deep into how you can download, configure, and secure your IoT P2P connections using Raspberry Pi.
As the IoT ecosystem expands, so does the need for secure communication channels. Protecting your devices from unauthorized access is critical to maintaining privacy and functionality. This guide will walk you through the steps required to establish a secure peer-to-peer (P2P) connection for remote IoT devices using Raspberry Pi, ensuring your setup remains free from vulnerabilities.
Whether you're a hobbyist or a professional developer, understanding the intricacies of secure IoT P2P connections is essential. This article covers everything from downloading the necessary software to configuring your Raspberry Pi for optimal performance. By the end of this guide, you'll have the knowledge and tools needed to securely connect remote IoT devices using a P2P setup.
Table of Contents
- Introduction to Secure IoT Connections
- Understanding Raspberry Pi Basics
- Why Secure P2P Connections Are Essential
- Downloading the Necessary Software
- Configuring Raspberry Pi for IoT P2P
- Implementing Security Measures
- Optimizing Performance
- Troubleshooting Common Issues
- Future Trends in IoT Security
- Conclusion and Call to Action
Introduction to Secure IoT Connections
IoT devices are revolutionizing industries by enabling smart homes, industrial automation, and healthcare monitoring. However, the security of these devices remains a top concern. Establishing a securely connect remote IoT P2P free environment is crucial to prevent unauthorized access and data breaches.
Understanding IoT Ecosystems
IoT ecosystems consist of interconnected devices that communicate via the internet. These devices collect and exchange data, making them vulnerable to cyber threats if not properly secured. Ensuring the security of IoT connections is vital for maintaining trust in the technology.
Importance of Peer-to-Peer (P2P) Connections
P2P connections eliminate the need for centralized servers, reducing latency and enhancing privacy. By using Raspberry Pi as a platform, you can create a secure P2P network for your IoT devices, ensuring data remains protected during transmission.
Understanding Raspberry Pi Basics
Raspberry Pi is a compact and affordable single-board computer that serves as an ideal platform for IoT projects. Its versatility and open-source nature make it a popular choice for developers seeking to implement secure IoT solutions.
Key Features of Raspberry Pi
- Low power consumption
- Support for multiple operating systems
- Extensive community support
- Compatibility with various sensors and modules
Choosing the Right Raspberry Pi Model
When selecting a Raspberry Pi model for your IoT project, consider factors such as processing power, memory, and connectivity options. The Raspberry Pi 4 Model B is a popular choice due to its advanced features and performance capabilities.
Why Secure P2P Connections Are Essential
Securing P2P connections is essential to protect sensitive data and prevent unauthorized access. In an IoT environment, where devices communicate directly with each other, ensuring the security of these connections is paramount.
Common Security Threats in IoT
- Malware attacks
- Data interception
- Unauthorized access
- Denial-of-service (DoS) attacks
Benefits of Secure P2P Connections
Implementing secure P2P connections offers several advantages, including enhanced privacy, reduced latency, and improved reliability. By using Raspberry Pi as a platform, you can create a secure network that meets the demands of modern IoT applications.
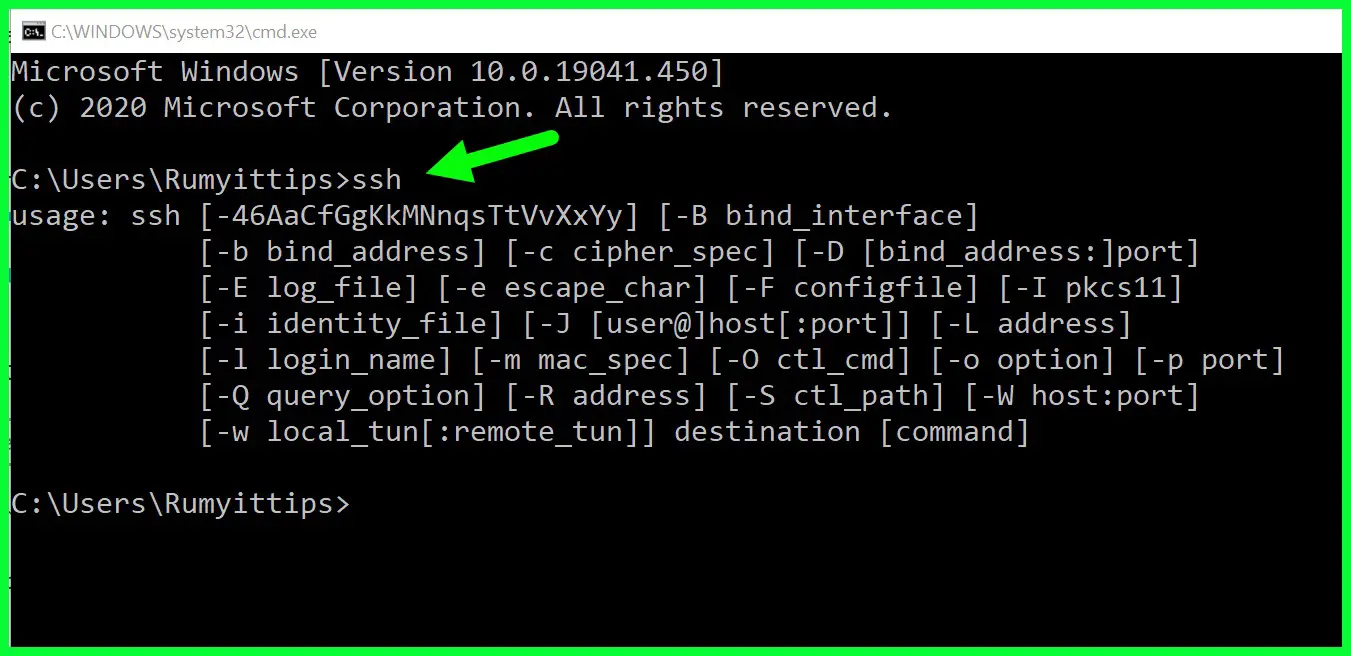
Downloading the Necessary Software
To securely connect remote IoT P2P free, you'll need to download and install the appropriate software on your Raspberry Pi. This section outlines the steps required to obtain the necessary tools and libraries.
Operating System Options
Raspberry Pi supports multiple operating systems, including Raspbian, Ubuntu, and specialized IoT-focused distributions. Choose an operating system that aligns with your project requirements and download the image file from the official website.
Installing Essential Libraries
Once the operating system is installed, you can install essential libraries for IoT communication. Popular choices include MQTT, CoAP, and WebSockets, which facilitate secure data exchange between devices.
Configuring Raspberry Pi for IoT P2P
Configuring your Raspberry Pi for IoT P2P involves setting up network parameters, enabling secure communication protocols, and optimizing performance settings.
Setting Up Network Parameters
Configure your Raspberry Pi to connect to your local network using Wi-Fi or Ethernet. Ensure that the device has a static IP address to facilitate consistent communication with other IoT devices.
Enabling Secure Communication Protocols
Implement encryption protocols such as TLS/SSL to secure data transmission between devices. Use certificates to authenticate devices and prevent unauthorized access to your network.
Implementing Security Measures
Securing your IoT P2P connections requires a multi-layered approach. This section explores various security measures you can implement to protect your Raspberry Pi-based IoT network.
Firewall Configuration
Set up a firewall to control incoming and outgoing network traffic. Use tools like iptables or ufw to define rules that restrict access to unauthorized devices and services.
Data Encryption Techniques
Encrypt sensitive data using strong encryption algorithms such as AES or RSA. Ensure that encryption keys are stored securely and regularly updated to maintain the integrity of your network.
Optimizing Performance
Optimizing the performance of your Raspberry Pi-based IoT network involves fine-tuning hardware settings, reducing latency, and maximizing resource utilization.
Hardware Optimization
Upgrade your Raspberry Pi's hardware components, such as memory and storage, to improve performance. Use external SSDs or USB drives for faster data access and enhanced reliability.
Reducing Latency
Minimize latency by optimizing network settings and using efficient communication protocols. Prioritize critical data packets and implement caching mechanisms to reduce the load on your network.
Troubleshooting Common Issues
Despite careful planning, issues may arise when setting up a secure IoT P2P network. This section provides solutions to common problems encountered during the configuration process.
Network Connectivity Issues
If your Raspberry Pi fails to connect to the network, check the Wi-Fi settings or Ethernet connection. Ensure that the device has the correct IP address and subnet mask configured.
Security Configuration Errors
Verify that all security settings, including encryption protocols and firewall rules, are correctly configured. Use diagnostic tools to identify and resolve any misconfigurations that may compromise the security of your network.
Future Trends in IoT Security
The future of IoT security lies in advancements such as blockchain technology, artificial intelligence, and quantum encryption. These innovations promise to enhance the security of IoT networks and provide robust protection against emerging threats.
Blockchain for IoT Security
Blockchain technology offers a decentralized approach to securing IoT devices. By using blockchain, you can create a tamper-proof ledger of transactions and ensure the integrity of your IoT network.
Artificial Intelligence in Threat Detection
AI-powered systems can analyze network traffic patterns and detect anomalies that may indicate a security breach. Implementing AI-based solutions can enhance the security of your IoT network and provide real-time threat detection capabilities.
Conclusion and Call to Action
Securing IoT P2P connections using Raspberry Pi is essential for maintaining the integrity and functionality of your network. By following the steps outlined in this guide, you can create a secure environment that protects your devices from cyber threats.
We encourage readers to share their experiences and insights in the comments section below. Your feedback helps us improve our content and provide valuable information to the community. Additionally, explore other articles on our website to deepen your understanding of IoT security and related topics.
References: