Connecting remote IoT devices securely has become a critical need in today's interconnected world. As more devices are integrated into our daily lives, ensuring secure communication between them is essential for privacy and functionality. The use of Raspberry Pi as a platform for IoT applications is gaining traction, especially when paired with Android devices for remote access. This guide will explore how to securely connect IoT devices using a P2P (Peer-to-Peer) network setup, leveraging Raspberry Pi and Android for seamless operation.
As technology continues to evolve, the Internet of Things (IoT) is transforming the way we interact with our environment. From smart homes to industrial automation, IoT devices are becoming indispensable. However, the challenge lies in maintaining secure connections, especially when these devices are accessed remotely. This article aims to address this challenge by providing a step-by-step guide to setting up a secure P2P connection using Raspberry Pi and Android.
Whether you're a tech enthusiast or a professional looking to enhance your IoT infrastructure, this article offers practical insights and actionable steps. We'll delve into the technical aspects of setting up a secure connection, explore the tools and software required, and provide tips to ensure maximum security. By the end of this guide, you'll have the knowledge and resources to implement a secure IoT P2P network.
Here is a quick overview of what we will cover:
- Understanding IoT and its security challenges
- Setting up Raspberry Pi for IoT applications
- Configuring P2P connections for secure communication
- Downloading and integrating Android apps for remote access
- Tips for enhancing security in IoT networks
Table of Contents
- Introduction to IoT and Security Challenges
- Setting Up Raspberry Pi for IoT Applications
- Configuring Secure P2P Connections
- Integrating Android for Remote Access
- Essential Software Tools for IoT
- Security Tips for IoT Networks
- Common Issues and Troubleshooting
- Real-World Applications of IoT P2P Networks
- Future Trends in IoT Security
- Conclusion and Call to Action
Introduction to IoT and Security Challenges
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity, enabling them to exchange data. While IoT offers numerous benefits, such as increased efficiency and convenience, it also poses significant security challenges. Devices connected to the internet are vulnerable to cyberattacks, data breaches, and unauthorized access. Therefore, securing IoT devices is paramount, especially when they are accessed remotely.
Key Security Challenges in IoT
Here are some of the primary security challenges associated with IoT:
- Data Privacy: Protecting sensitive information transmitted between devices.
- Device Authentication: Ensuring only authorized devices can communicate.
- Network Security: Preventing unauthorized access to the network.
Setting Up Raspberry Pi for IoT Applications
Raspberry Pi is a popular choice for IoT projects due to its affordability, flexibility, and ease of use. Setting up Raspberry Pi involves installing the necessary operating system, configuring network settings, and installing required software. Below are the steps to get started:
Step-by-Step Raspberry Pi Setup
- Install Raspberry Pi OS on your microSD card.
- Connect Raspberry Pi to your network via Ethernet or Wi-Fi.
- Update the operating system and install required packages.
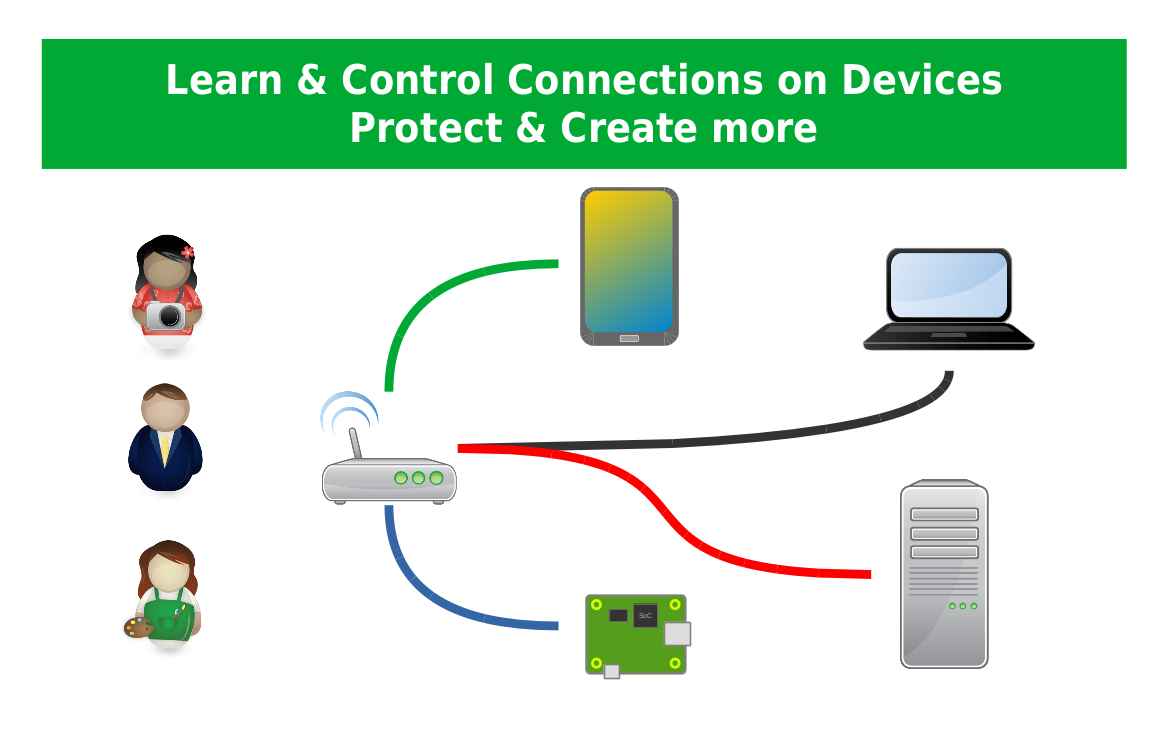
Configuring Secure P2P Connections
Peer-to-Peer (P2P) connections allow devices to communicate directly without relying on a central server. This setup enhances security by reducing the attack surface and ensuring direct communication between devices.
Steps to Configure P2P Connections
Here are the steps to configure a secure P2P connection:
- Set up a private key infrastructure for device authentication.
- Use secure communication protocols such as TLS or SSH.
- Implement firewalls to restrict unauthorized access.
Integrating Android for Remote Access
Android devices offer a convenient way to access IoT networks remotely. By downloading and installing the appropriate apps, users can monitor and control their IoT devices from anywhere. Below are some popular Android apps for IoT:
Popular Android Apps for IoT
- Home Assistant
- Blynk
- ThingSpeak
Essential Software Tools for IoT
Several software tools are essential for building and maintaining a secure IoT network. These tools help with device management, data analytics, and security monitoring. Below are some of the most widely used tools:
Top IoT Software Tools
- Node-RED
- MQTT
- OpenHAB
Security Tips for IoT Networks
Ensuring the security of your IoT network requires a proactive approach. Here are some tips to enhance security:
Best Practices for IoT Security
- Regularly update firmware and software.
- Use strong passwords and enable two-factor authentication.
- Monitor network activity for suspicious behavior.
Common Issues and Troubleshooting
Even with careful planning, issues can arise when setting up an IoT network. Below are some common problems and their solutions:
Troubleshooting IoT Connections
- Connection Drops: Check network settings and restart devices.
- Device Incompatibility: Ensure all devices are using compatible protocols.
- Security Breaches: Review security logs and update security measures.
Real-World Applications of IoT P2P Networks
IoT P2P networks have numerous real-world applications, ranging from smart homes to industrial automation. Below are some examples:
Applications of IoT P2P Networks
- Smart Home Automation
- Industrial Monitoring
- Healthcare Devices
Future Trends in IoT Security
The future of IoT security lies in adopting advanced technologies such as blockchain, AI, and machine learning. These technologies offer enhanced security features and improved threat detection capabilities. As IoT continues to evolve, staying updated with the latest trends is crucial for maintaining secure networks.
Conclusion and Call to Action
In conclusion, securely connecting remote IoT devices using a P2P network with Raspberry Pi and Android is both feasible and practical. By following the steps outlined in this guide, you can set up a secure and efficient IoT network. Remember to prioritize security and regularly update your systems to protect against emerging threats.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, explore other articles on our site to deepen your understanding of IoT and related technologies. Together, let's build a safer and more connected world.