In today's digital age, remote IoT monitoring through SSH download has become a crucial aspect of managing devices and systems across various industries. Whether you're a tech enthusiast, a business owner, or an IT professional, understanding this technology is essential for optimizing operations and enhancing security. RemoteIoT monitoring allows users to access, control, and manage IoT devices from anywhere in the world, ensuring seamless connectivity and efficient performance.
The Internet of Things (IoT) continues to revolutionize how we interact with technology, enabling devices to communicate and share data effortlessly. However, with the increasing number of connected devices, monitoring and securing these systems remotely have become more complex. This is where SSH (Secure Shell) comes into play, offering a secure method for remote access and management.
This comprehensive guide will explore everything you need to know about remote IoT monitoring through SSH download. From understanding the basics of SSH to implementing advanced monitoring techniques, we'll cover it all. By the end of this article, you'll have a thorough understanding of how to leverage this technology for your needs.
Table of Contents
- Introduction to SSH
- Importance of Remote IoT Monitoring
- How SSH Works
- Benefits of Remote IoT Monitoring
- Setting Up SSH for Remote IoT Monitoring
- Best Practices for Secure SSH Connections
- Tools for Remote IoT Monitoring
- Common Issues and Troubleshooting
- Future of Remote IoT Monitoring
- Conclusion and Call to Action
Introduction to SSH
Secure Shell (SSH) is a cryptographic network protocol that facilitates secure communication between devices over an unsecured network. Originally developed in 1995, SSH has become the standard for remote access and administration of servers, routers, and IoT devices. In the context of remote IoT monitoring, SSH plays a critical role in enabling secure connections, allowing administrators to manage devices without compromising data integrity.
SSH operates on port 22 by default and uses encryption algorithms to protect data transmitted between the client and server. This ensures that sensitive information, such as login credentials and system data, remains confidential during transmission. Additionally, SSH supports authentication methods like passwords, public key authentication, and multi-factor authentication (MFA), providing robust security measures for remote access.
Why SSH is Essential for IoT Devices
IoT devices often operate in diverse environments, making them vulnerable to cyber threats. SSH offers a secure solution for managing these devices remotely, reducing the risk of unauthorized access and data breaches. By implementing SSH for remote IoT monitoring, organizations can:
- Ensure secure communication between devices and servers.
- Automate routine tasks and updates without physical intervention.
- Monitor device performance in real-time and address issues promptly.
Importance of Remote IoT Monitoring
Remote IoT monitoring is vital for maintaining the efficiency and security of connected devices. With the proliferation of IoT devices across industries, including healthcare, manufacturing, and agriculture, monitoring these systems remotely has become essential for optimizing operations and ensuring reliability.
Key Benefits of Remote IoT Monitoring
Here are some of the key benefits of implementing remote IoT monitoring:
- Improved Efficiency: Automate routine tasks and reduce manual intervention, saving time and resources.
- Enhanced Security: Monitor devices for suspicious activity and implement security measures to prevent breaches.
- Real-Time Data Access: Access critical data from anywhere, enabling informed decision-making.
- Cost Savings: Minimize downtime and maintenance costs by addressing issues proactively.
How SSH Works
SSH operates using a client-server model, where the client initiates a connection to the server. During the connection process, SSH performs several steps to ensure secure communication:
- Connection Establishment: The client connects to the server using the SSH protocol.
- Key Exchange: The client and server exchange cryptographic keys to establish a secure session.
- Authentication: The client authenticates with the server using a password, public key, or other methods.
- Encrypted Communication: Once authenticated, all data transmitted between the client and server is encrypted, ensuring confidentiality.
SSH Protocols and Versions
SSH has two primary versions: SSH-1 and SSH-2. While SSH-1 was the original protocol, SSH-2 is now the standard due to its improved security features. SSH-2 supports stronger encryption algorithms and better authentication methods, making it the preferred choice for remote IoT monitoring.
Benefits of Remote IoT Monitoring
Implementing remote IoT monitoring offers numerous advantages for businesses and individuals alike. From enhancing operational efficiency to improving security, the benefits are significant:
- Scalability: Easily manage large numbers of IoT devices from a centralized location.
- Flexibility: Access devices from anywhere using a variety of platforms and devices.
- Automation: Automate routine tasks, such as firmware updates and configuration changes.
- Proactive Maintenance: Monitor device performance and address issues before they escalate.
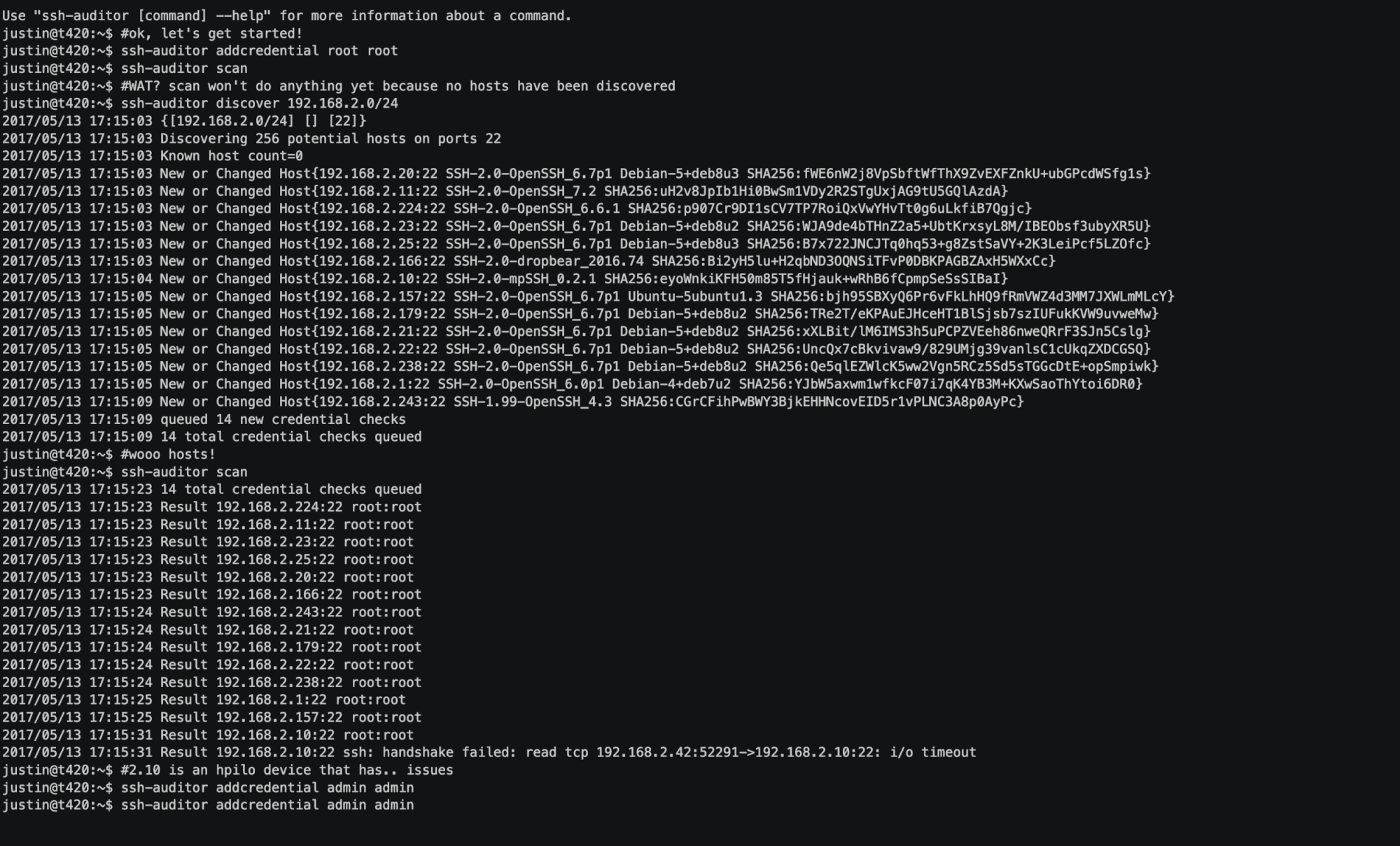
Setting Up SSH for Remote IoT Monitoring
Setting up SSH for remote IoT monitoring involves several steps. Below is a step-by-step guide to help you configure SSH securely:
- Install SSH Server: Install an SSH server on the IoT device or server you want to monitor.
- Generate SSH Keys: Create public and private key pairs for authentication.
- Configure SSH Settings: Modify SSH configuration files to enhance security and customize settings.
- Test the Connection: Use an SSH client to connect to the server and ensure the setup is functioning correctly.
Best SSH Clients for Remote IoT Monitoring
Several SSH clients are available for remote IoT monitoring, each with its own set of features and capabilities. Some popular options include:
- PuTTY: A free and widely used SSH client for Windows.
- OpenSSH: A robust, open-source SSH client available on most Linux and macOS systems.
- MobaxTerm: A powerful terminal emulator and SSH client for Windows, offering advanced features like file transfer and session management.
Best Practices for Secure SSH Connections
Ensuring secure SSH connections is crucial for protecting IoT devices and data. Follow these best practices to enhance security:
- Use Strong Passwords: Avoid using weak or default passwords for SSH access.
- Enable Public Key Authentication: Replace password-based authentication with public key authentication for added security.
- Disable Root Login: Restrict root access to prevent unauthorized users from gaining administrative privileges.
- Monitor Connection Attempts: Regularly review logs for suspicious activity and block malicious IP addresses.
SSH Security Tips
In addition to the best practices mentioned above, consider implementing the following security tips:
- Use a Non-Standard Port: Change the default SSH port (22) to a non-standard port to reduce automated attacks.
- Implement Firewall Rules: Configure firewalls to restrict SSH access to trusted IP addresses.
- Regularly Update Software: Keep SSH servers and clients up to date with the latest security patches.
Tools for Remote IoT Monitoring
Several tools are available to facilitate remote IoT monitoring through SSH. These tools offer advanced features for managing and monitoring IoT devices:
- Node-RED: A visual programming tool for wiring together IoT devices and services.
- ThingsBoard: An open-source IoT platform for device management and data visualization.
- Home Assistant: A popular home automation platform that supports SSH integration for remote monitoring.
Choosing the Right Tool
When selecting a tool for remote IoT monitoring, consider the following factors:
- Scalability: Ensure the tool can handle the number of devices you plan to monitor.
- Compatibility: Verify that the tool supports your specific IoT devices and platforms.
- Security Features: Look for tools that offer robust security measures, such as encryption and multi-factor authentication.
Common Issues and Troubleshooting
While SSH is a reliable protocol, issues can arise during setup and operation. Below are some common problems and solutions:
- Connection Refused: Ensure the SSH server is running and the firewall allows SSH traffic.
- Authentication Failure: Verify that the correct username and password or SSH key are being used.
- Timeout Errors: Check network connectivity and increase the SSH timeout settings if necessary.
Troubleshooting Tips
To resolve SSH-related issues, follow these troubleshooting tips:
- Review Logs: Check server logs for error messages and diagnostic information.
- Test with a Different Client: Use an alternative SSH client to rule out client-side issues.
- Reconfigure SSH Settings: Modify SSH configuration files to address specific problems.
Future of Remote IoT Monitoring
As IoT technology continues to evolve, remote IoT monitoring will play an increasingly important role in managing connected devices. Advances in artificial intelligence, machine learning, and edge computing will enhance the capabilities of remote monitoring systems, enabling more intelligent and autonomous operations.
Trends in Remote IoT Monitoring
Some key trends shaping the future of remote IoT monitoring include:
- AI-Powered Analytics: Leveraging AI to analyze IoT data and provide actionable insights.
- Edge Computing: Processing data closer to the source for faster response times and reduced latency.
- 5G Connectivity: Utilizing 5G networks to enable faster and more reliable remote monitoring.
Conclusion and Call to Action
Remote IoT monitoring through SSH download is a powerful tool for managing and securing connected devices. By understanding the basics of SSH and implementing best practices for secure connections, you can harness the full potential of this technology. Whether you're monitoring home automation systems or industrial IoT devices, SSH provides a reliable and secure solution for remote access and management.
We encourage you to take action by exploring the tools and techniques discussed in this guide. Share your experiences and insights in the comments below, and don't hesitate to reach out if you have any questions. For more in-depth information on IoT and related technologies, explore our other articles and resources.