Remote IoT VPC SSH Raspberry Pi has become a popular topic among tech enthusiasts, professionals, and hobbyists alike. As the world moves towards more connected systems, understanding how to manage and secure remote IoT devices is crucial. This article dives deep into the subject, offering valuable insights, tips, and best practices for setting up and maintaining a secure connection using SSH on a Raspberry Pi within a Virtual Private Cloud (VPC).
In today's digital age, the Internet of Things (IoT) has transformed the way we interact with technology. From smart homes to industrial automation, IoT devices are everywhere. However, managing these devices remotely while ensuring their security can be challenging. This is where Remote IoT VPC SSH Raspberry Pi comes into play, providing a reliable solution for remote access and control.
Whether you're a beginner or an experienced developer, this guide will equip you with the knowledge and tools necessary to set up and manage your IoT projects effectively. Let's explore how you can leverage this technology to enhance your projects and improve efficiency.
Table of Contents
- Introduction to Remote IoT VPC
- Raspberry Pi Overview
- SSH and Its Importance
- Why Use VPC for Remote IoT?
- Step-by-Step Setup Guide
- Best Practices for Remote IoT
- Common Issues and Troubleshooting
- Case Studies and Examples
- Future of Remote IoT VPC SSH
- Conclusion and Call to Action
Introduction to Remote IoT VPC
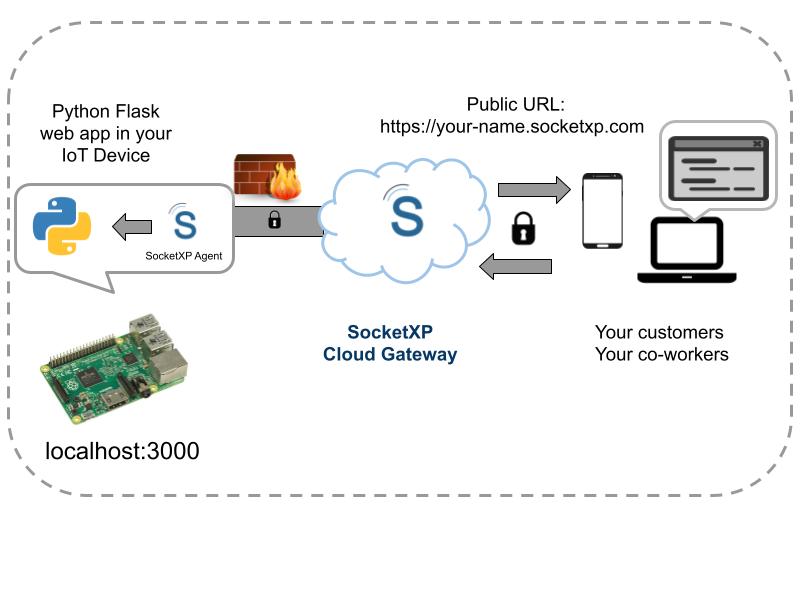
Remote IoT VPC (Virtual Private Cloud) is a powerful combination that allows users to manage IoT devices securely from anywhere in the world. By leveraging VPC, you create a private network environment that isolates your devices from the public internet, reducing the risk of unauthorized access. This setup is particularly beneficial for businesses and individuals who rely on IoT devices for critical operations.
SSH (Secure Shell) plays a vital role in this setup by providing a secure method of communication between your local machine and the IoT devices. It encrypts data transmitted over the network, ensuring that sensitive information remains protected.
Understanding the basics of Remote IoT VPC SSH Raspberry Pi is essential for anyone looking to enhance their IoT projects. This section will provide an overview of the key components involved and their significance in creating a robust remote access system.
Raspberry Pi Overview
Raspberry Pi is a versatile single-board computer that has gained immense popularity among developers, educators, and hobbyists. Its affordability, compact size, and flexibility make it an ideal choice for IoT projects. The Raspberry Pi can be configured to act as a server, gateway, or even a client device in a remote IoT setup.
When combined with SSH and VPC, the Raspberry Pi becomes a powerful tool for managing remote IoT devices. Its ability to run lightweight operating systems like Raspbian and support various programming languages makes it suitable for a wide range of applications.
Here are some key features of Raspberry Pi:
- Compact and lightweight design
- Supports multiple operating systems
- Low power consumption
- Highly customizable
SSH and Its Importance
SSH (Secure Shell) is a network protocol that provides secure communication between devices over an unsecured network. It is widely used for remote command-line login and execution, file transfer, and tunneling. In the context of Remote IoT VPC SSH Raspberry Pi, SSH ensures that data transmitted between your local machine and the IoT devices remains encrypted and protected from unauthorized access.
Here are some reasons why SSH is crucial for remote IoT setups:
- Data encryption to prevent eavesdropping
- Authentication mechanisms to verify user identity
- Secure file transfer capabilities
- Support for port forwarding and tunneling
Why Use VPC for Remote IoT?
A Virtual Private Cloud (VPC) offers a secure and isolated environment for managing IoT devices. By setting up a VPC, you create a private network within the public cloud, allowing you to control access to your devices and protect them from potential threats. This is especially important for remote IoT setups where devices are accessed over the internet.
Here are some benefits of using VPC for remote IoT:
- Enhanced security through network isolation
- Flexible network configuration options
- Scalability to accommodate growing IoT projects
- Improved performance through optimized routing
Step-by-Step Setup Guide
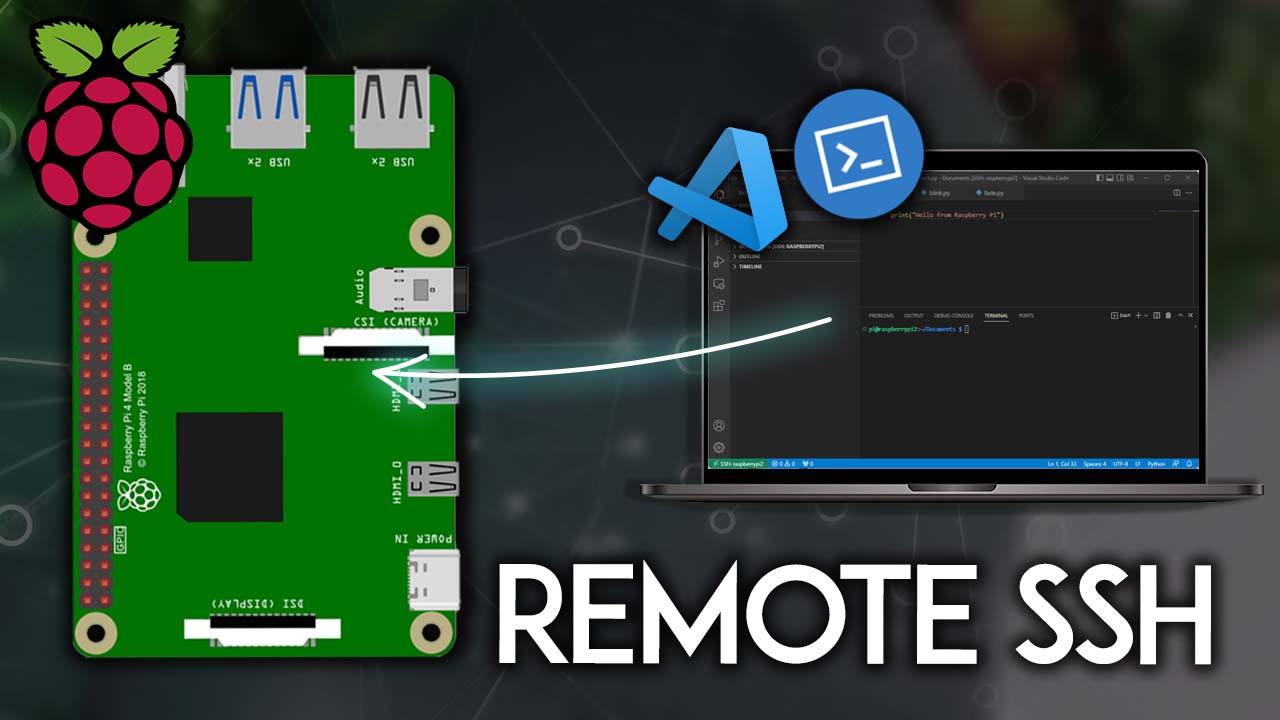
Installing SSH on Raspberry Pi
Setting up SSH on your Raspberry Pi is a straightforward process. Follow these steps to enable SSH on your device:
- Connect your Raspberry Pi to a monitor, keyboard, and mouse.
- Power on the device and log in to the operating system.
- Open the terminal and type the following command to enable SSH:
sudo raspi-config. - Navigate to the "Interfacing Options" menu and select "SSH."
- Choose "Yes" to enable SSH and then reboot your device.
Configuring VPC Settings
Configuring your VPC involves setting up a private network and defining access rules. Here's how you can do it:
- Log in to your cloud provider's console (e.g., AWS, Google Cloud).
- Create a new VPC and define its CIDR block.
- Add subnets and configure routing tables.
- Set up security groups to control inbound and outbound traffic.
- Associate your Raspberry Pi with the VPC by assigning it a private IP address.
Securing Your SSH Connection
Securing your SSH connection is essential to protect your IoT devices from unauthorized access. Here are some best practices to enhance security:
- Use strong and unique passwords for SSH authentication.
- Enable two-factor authentication (2FA) for added security.
- Disable root login to prevent direct access to the system.
- Limit SSH access to specific IP addresses using firewall rules.
Best Practices for Remote IoT
Implementing best practices for remote IoT setups can significantly improve the security and reliability of your system. Here are some tips to consider:
- Regularly update your Raspberry Pi's operating system and software.
- Monitor network activity for suspicious behavior.
- Use encryption for all data transmissions.
- Implement access controls to restrict who can access your devices.
Common Issues and Troubleshooting
Despite careful planning, issues can arise when setting up a Remote IoT VPC SSH Raspberry Pi system. Here are some common problems and their solutions:
- SSH Connection Refused: Check your firewall settings and ensure that the SSH port is open.
- Slow Network Performance: Optimize your VPC configuration and reduce unnecessary traffic.
- Device Disconnections: Ensure stable internet connectivity and configure auto-reconnect settings.
Case Studies and Examples
Real-world examples can provide valuable insights into the practical applications of Remote IoT VPC SSH Raspberry Pi. Here are a few case studies:
- Smart Agriculture: Farmers use IoT sensors connected to Raspberry Pi devices to monitor soil moisture levels and automate irrigation systems.
- Remote Monitoring: Companies deploy IoT cameras with Raspberry Pi as a gateway to monitor industrial equipment in real-time.
- Home Automation: Individuals use IoT devices controlled by Raspberry Pi to manage lighting, climate control, and security systems in their homes.
Future of Remote IoT VPC SSH
The future of Remote IoT VPC SSH Raspberry Pi looks promising as technology continues to evolve. Advancements in AI, machine learning, and edge computing will further enhance the capabilities of IoT systems. As more devices become connected, the need for secure and efficient remote access solutions will only increase.
Staying updated with the latest trends and technologies in the IoT space will be crucial for anyone involved in this field. Continuous learning and adaptation will ensure that your projects remain at the forefront of innovation.
Conclusion and Call to Action
In conclusion, Remote IoT VPC SSH Raspberry Pi offers a powerful and secure solution for managing IoT devices remotely. By following the steps outlined in this guide, you can set up and maintain a robust system that meets your project requirements. Remember to adhere to best practices and regularly update your setup to ensure optimal performance and security.
We invite you to share your thoughts and experiences in the comments section below. Have you implemented a similar setup? What challenges did you face, and how did you overcome them? Additionally, feel free to explore other articles on our site for more insights into IoT and related technologies.
Thank you for reading, and happy tinkering!