In today's hyper-connected world, Best RemoteIoT SSH plays a critical role in ensuring secure communication between devices and networks. As more businesses adopt IoT technologies, securing these connections has become paramount to protect sensitive data and prevent cyberattacks. This article delves into the importance of using SSH for remote IoT management and explores the best practices for implementing it effectively.
IoT devices are revolutionizing industries by enabling smarter, more efficient operations. However, with the rise in connectivity comes an increased risk of security breaches. RemoteIoT SSH provides a secure channel for managing and monitoring IoT devices from anywhere in the world, making it an essential tool for modern IT professionals.
This article will guide you through the fundamentals of RemoteIoT SSH, its benefits, and how to implement it in your IoT infrastructure. By the end, you'll have a thorough understanding of why Best RemoteIoT SSH is crucial for safeguarding your IoT ecosystem.
Table of Contents
- What is RemoteIoT SSH?
- The Importance of Best RemoteIoT SSH
- Benefits of Using SSH for IoT
- How to Set Up RemoteIoT SSH
- Best Practices for Secure RemoteIoT SSH
- Common Security Issues in IoT
- Top Tools for RemoteIoT SSH
- Case Studies: Real-World Examples of RemoteIoT SSH
- The Future of Best RemoteIoT SSH
- Conclusion
What is RemoteIoT SSH?
RemoteIoT SSH refers to the use of Secure Shell (SSH) protocols to manage and monitor IoT devices remotely. SSH is a network protocol that provides encrypted communication between devices, ensuring that data transmitted over the internet remains secure. By leveraging RemoteIoT SSH, organizations can control their IoT infrastructure from anywhere, reducing the need for physical access to devices.
How Does SSH Work in IoT?
SSH operates by creating a secure tunnel between a client and a server. In the context of IoT, this means that administrators can connect to IoT devices securely, execute commands, and transfer files without exposing sensitive information to potential threats. The protocol uses cryptographic techniques to authenticate users and encrypt data, making it one of the most reliable methods for securing IoT communications.
The Importance of Best RemoteIoT SSH
As IoT continues to expand, the need for robust security measures becomes increasingly critical. Best RemoteIoT SSH is vital for protecting IoT networks from unauthorized access and cyberattacks. By implementing SSH, organizations can:
- Ensure secure communication between devices
- Authenticate users and devices
- Encrypt sensitive data
- Remotely manage IoT devices without compromising security
Benefits of Using SSH for IoT
Adopting SSH for IoT management offers numerous advantages, including:
Enhanced Security
SSH encrypts all data transmitted between devices, making it nearly impossible for attackers to intercept or manipulate the information. This level of security is essential for safeguarding sensitive data and maintaining the integrity of IoT networks.
Remote Access
With SSH, administrators can access and manage IoT devices from anywhere in the world. This flexibility allows for faster troubleshooting and more efficient operations, reducing downtime and improving productivity.
Cost Efficiency
Implementing SSH eliminates the need for physical access to IoT devices, saving organizations time and money. It also reduces the risk of human error, which can lead to costly security breaches.
How to Set Up RemoteIoT SSH
Setting up RemoteIoT SSH involves several steps, including configuring SSH servers, generating keys, and establishing secure connections. Below is a step-by-step guide to help you get started:
- Install an SSH server on your IoT device
- Generate public and private keys for authentication
- Configure firewall settings to allow SSH traffic
- Test the connection to ensure secure communication
Best Practices for Secure RemoteIoT SSH
To maximize the security benefits of RemoteIoT SSH, follow these best practices:
- Use strong, unique passwords for authentication
- Enable two-factor authentication (2FA) for added security
- Regularly update SSH software to address vulnerabilities
- Monitor SSH logs for suspicious activity
Common Security Issues in IoT
Despite the advantages of RemoteIoT SSH, IoT networks face several security challenges. Some of the most common issues include:
Weak Authentication
Many IoT devices come with default passwords that are easily guessed or cracked by attackers. Organizations must implement strong authentication mechanisms to prevent unauthorized access.
Unpatched Vulnerabilities
Failure to update firmware and software leaves IoT devices vulnerable to exploitation. Regularly applying security patches is essential for maintaining a secure IoT environment.
Data Privacy Concerns
IoT devices often collect sensitive data, raising concerns about privacy and compliance with regulations such as GDPR. Implementing encryption and secure communication protocols like SSH helps protect this data.
Top Tools for RemoteIoT SSH
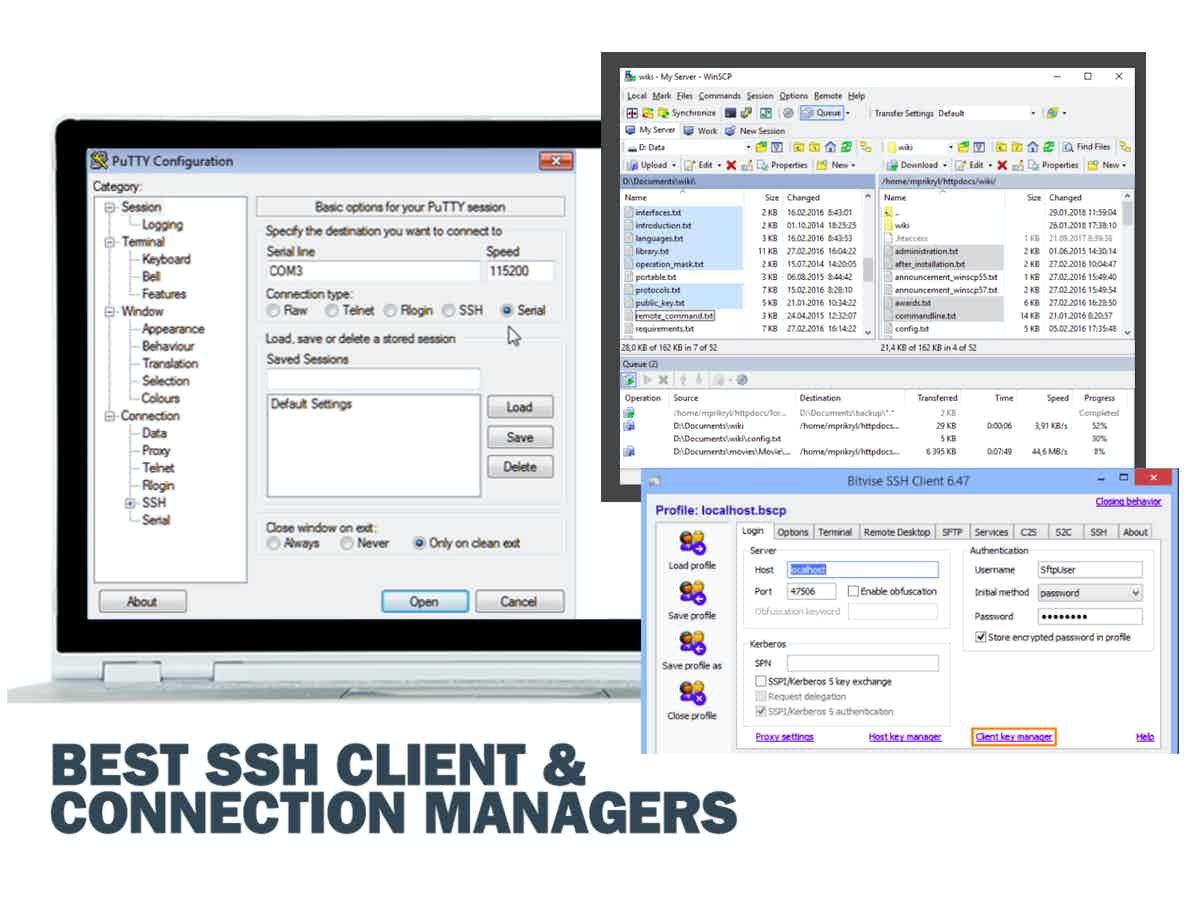
Several tools and platforms are available to facilitate RemoteIoT SSH implementation. Some of the most popular options include:
- OpenSSH: A widely used open-source SSH software suite
- Putty: A free SSH client for Windows users
- SSHFS: A file system client that allows secure mounting of remote directories
Case Studies: Real-World Examples of RemoteIoT SSH
Several organizations have successfully implemented RemoteIoT SSH to enhance their IoT security. For example:
Case Study 1: Smart Manufacturing
A manufacturing company used RemoteIoT SSH to secure its industrial IoT devices, enabling remote monitoring and maintenance of machinery. This resulted in reduced downtime and improved operational efficiency.
Case Study 2: Smart Agriculture
Agricultural businesses adopted RemoteIoT SSH to manage IoT sensors and devices in remote locations, ensuring real-time data collection and analysis without compromising security.
The Future of Best RemoteIoT SSH
As IoT continues to evolve, the role of RemoteIoT SSH will become even more significant. Emerging technologies such as quantum encryption and blockchain could further enhance the security of SSH protocols, providing even stronger protection for IoT networks. Staying informed about these advancements is crucial for organizations looking to maintain a secure IoT infrastructure.
Conclusion
Best RemoteIoT SSH is an indispensable tool for securing IoT networks and ensuring the safe transmission of data. By understanding its importance, implementing best practices, and leveraging the right tools, organizations can protect their IoT ecosystems from potential threats. We encourage readers to share their thoughts and experiences in the comments section below and explore other articles on our site for more insights into IoT security.
Remember, securing your IoT devices is not just a technical necessity—it's a business imperative. Take action today to safeguard your network and stay ahead of the curve in the ever-evolving world of IoT.