Are you looking to securely connect to your RemoteIoT device via SSH? If so, you're in the right place. This article will guide you step-by-step through the process of setting up and managing SSH connections for your RemoteIoT device.
In today's interconnected world, managing IoT devices remotely is crucial for efficiency and convenience. With the growing demand for smart solutions, understanding how to securely access and manage your RemoteIoT device via SSH is more important than ever.
This RemoteIoT device SSH tutorial is designed for beginners and professionals alike, providing actionable insights and best practices to ensure a secure and efficient setup. Whether you're configuring your first IoT device or optimizing your current setup, this guide has everything you need to get started.
Table of Contents
- Introduction to RemoteIoT Device SSH
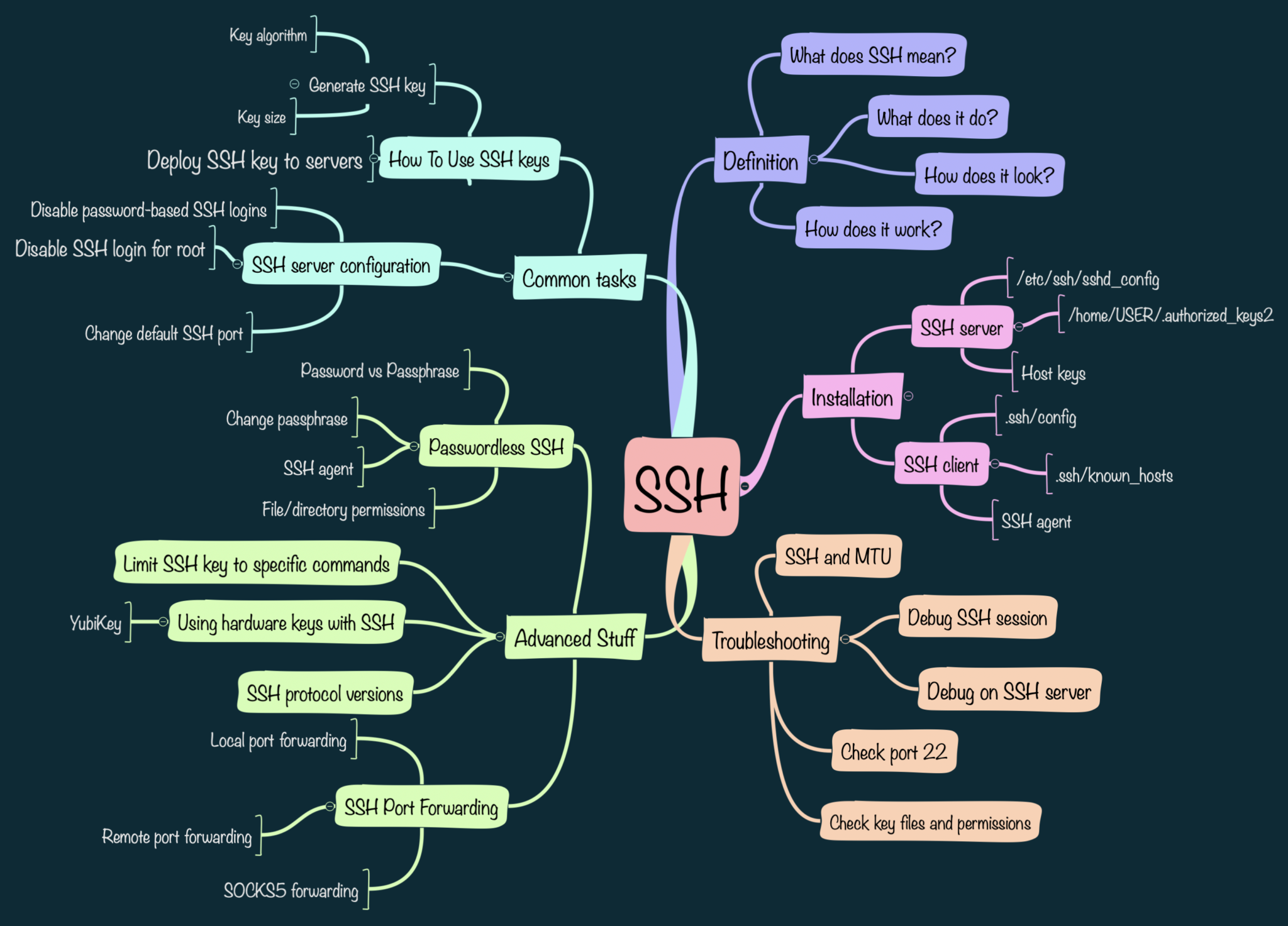
- What is SSH?
- Overview of RemoteIoT Devices
- Preparation for SSH Connection
- Step-by-Step SSH Setup
- Security Tips for RemoteIoT SSH
- Troubleshooting Common Issues
- Optimizing SSH Performance
- Alternatives to SSH for RemoteIoT Devices
- Conclusion and Next Steps
Introduction to RemoteIoT Device SSH
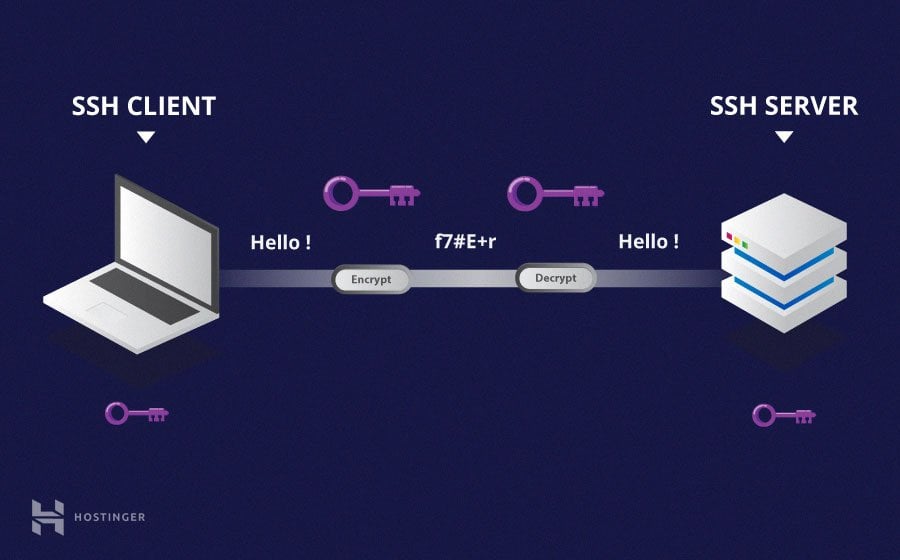
SSH, or Secure Shell, is a protocol designed to securely connect to remote devices over an unsecured network. When it comes to managing RemoteIoT devices, SSH provides a robust solution for secure communication and administration.
Using SSH for your RemoteIoT device ensures that your data remains encrypted and protected from unauthorized access. This tutorial will walk you through the entire process, from installation to optimization, ensuring that your IoT setup is both secure and efficient.
What is SSH?
SSH, or Secure Shell, is a cryptographic network protocol that facilitates secure communication between a client and a server. It is widely used for remote administration and file transfer in various industries.
Key features of SSH include:
- Data encryption to protect sensitive information
- Authentication mechanisms to verify user identity
- Support for secure file transfers via SCP and SFTP
For RemoteIoT devices, SSH serves as a critical tool for maintaining secure and reliable connections, ensuring that your IoT infrastructure operates seamlessly.
Overview of RemoteIoT Devices
RemoteIoT devices are part of the Internet of Things ecosystem, designed to operate and communicate over networks without requiring human intervention. These devices are commonly used in industries such as agriculture, healthcare, and manufacturing to automate processes and collect data.
When managing RemoteIoT devices, SSH offers a secure method to access and control them remotely. This ensures that even when devices are located in remote areas, administrators can still manage them effectively and securely.
Preparation for SSH Connection
Before diving into the SSH setup process, it's essential to prepare your environment properly. This includes gathering necessary tools and ensuring your RemoteIoT device is ready for secure connections.
Here are the steps to prepare:
- Ensure your RemoteIoT device has an active internet connection
- Verify that SSH is supported on your device
- Obtain the IP address of your RemoteIoT device
- Install an SSH client on your computer (e.g., PuTTY for Windows or Terminal for macOS/Linux)
Step-by-Step SSH Setup
Install SSH on Your RemoteIoT Device
The first step in setting up SSH for your RemoteIoT device is to ensure that the SSH server is installed and running. Most modern IoT devices come with SSH pre-installed, but if it's not, you'll need to install it manually.
Here's how to install SSH:
- Log in to your RemoteIoT device's operating system
- Run the following command to install SSH:
sudo apt-get install openssh-server - Restart the SSH service using:
sudo service ssh restart
Configure Firewall for SSH
Once SSH is installed, it's crucial to configure your firewall to allow SSH traffic. This ensures that your device remains secure while enabling remote access.
To configure the firewall:
- Open your firewall management tool
- Allow traffic on port 22 (default SSH port)
- Test the connection to ensure the firewall is not blocking SSH traffic
Security Tips for RemoteIoT SSH
Security is paramount when managing RemoteIoT devices via SSH. Below are some best practices to enhance the security of your SSH setup:
- Change the default SSH port to a non-standard port
- Disable root login to prevent unauthorized access
- Use strong, unique passwords or SSH keys for authentication
- Enable two-factor authentication (2FA) for added security
Implementing these security measures will significantly reduce the risk of unauthorized access to your RemoteIoT device.
Troubleshooting Common Issues
Even with proper setup, issues can arise when using SSH for your RemoteIoT device. Below are some common problems and their solutions:
- Connection refused: Ensure the SSH service is running and the firewall allows traffic on the correct port.
- Authentication failure: Verify your login credentials or SSH keys and ensure they are correctly configured.
- Timeout errors: Check your network connection and ensure the device's IP address is correct.
Optimizing SSH Performance
To ensure optimal performance of your RemoteIoT device's SSH connection, consider the following tips:
- Use compression to reduce data transfer size
- Limit the number of simultaneous connections to avoid overload
- Regularly update your SSH client and server software
By optimizing your SSH setup, you can improve the speed and reliability of your RemoteIoT device's remote management capabilities.
Alternatives to SSH for RemoteIoT Devices
While SSH is a popular choice for securing remote connections, there are alternative methods worth exploring:
- VPN: Virtual Private Networks provide secure tunnels for remote access
- Web-based interfaces: Some RemoteIoT devices offer secure web-based management tools
- MQTT: Message Queuing Telemetry Transport is another protocol used for IoT device communication
Each method has its advantages and disadvantages, so it's important to choose the one that best fits your needs.
Conclusion and Next Steps
In conclusion, managing your RemoteIoT device via SSH is a secure and efficient way to maintain remote control over your IoT infrastructure. By following the steps outlined in this tutorial, you can set up, secure, and optimize your SSH connections effectively.
We encourage you to take action by trying out the steps mentioned in this RemoteIoT device SSH tutorial. Leave a comment below if you have any questions or share this article with others who might find it useful. For further reading, explore our other articles on IoT security and management.
Remember, staying informed and proactive is key to maintaining a secure and efficient IoT setup. Thank you for reading, and happy tinkering!