In the era of digital transformation, ensuring robust network security has become more critical than ever, especially with the growing adoption of IoT devices. Remote IoT firewalls are essential tools that protect your network from unauthorized access and cyber threats. If you're looking for the best remote IoT firewall examples, this article will guide you through the top options available in the market.
As the Internet of Things (IoT) continues to expand, securing connected devices has become a top priority for businesses and individuals alike. With remote IoT firewalls, you can safeguard your network infrastructure without compromising performance or usability.
This article provides an in-depth exploration of the best remote IoT firewall examples, offering practical insights and actionable advice to help you make an informed decision. Whether you're a tech enthusiast, IT professional, or a business owner, this guide is tailored to meet your security needs.
Table of Contents
- Introduction to Remote IoT Firewalls
- Why Remote IoT Firewalls Are Important
- Criteria for Selecting the Best Remote IoT Firewall
- Top Remote IoT Firewall Examples
- Biometric Integration in IoT Firewalls
- Comparing Key Features
- Enhancing Network Security with IoT Firewalls
- Implementation Best Practices
- The Future of Remote IoT Firewalls
- Conclusion and Call to Action
Introduction to Remote IoT Firewalls
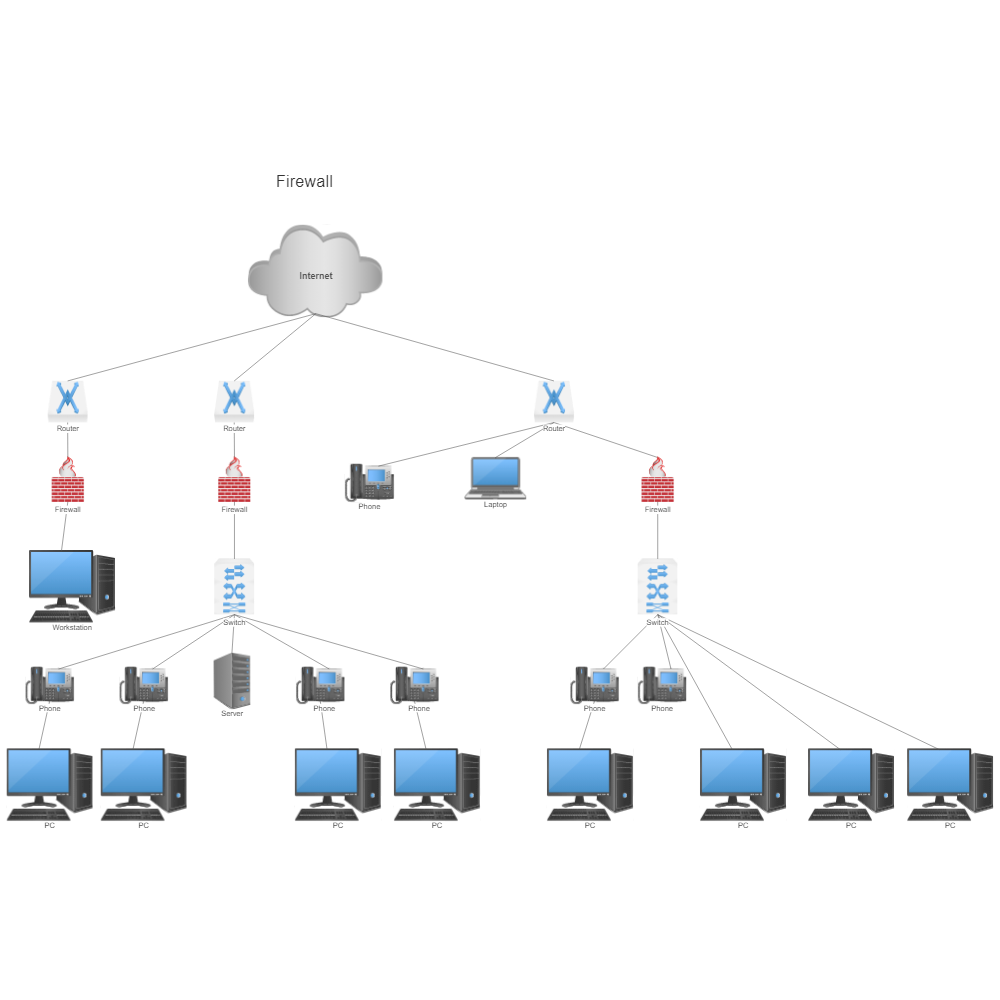
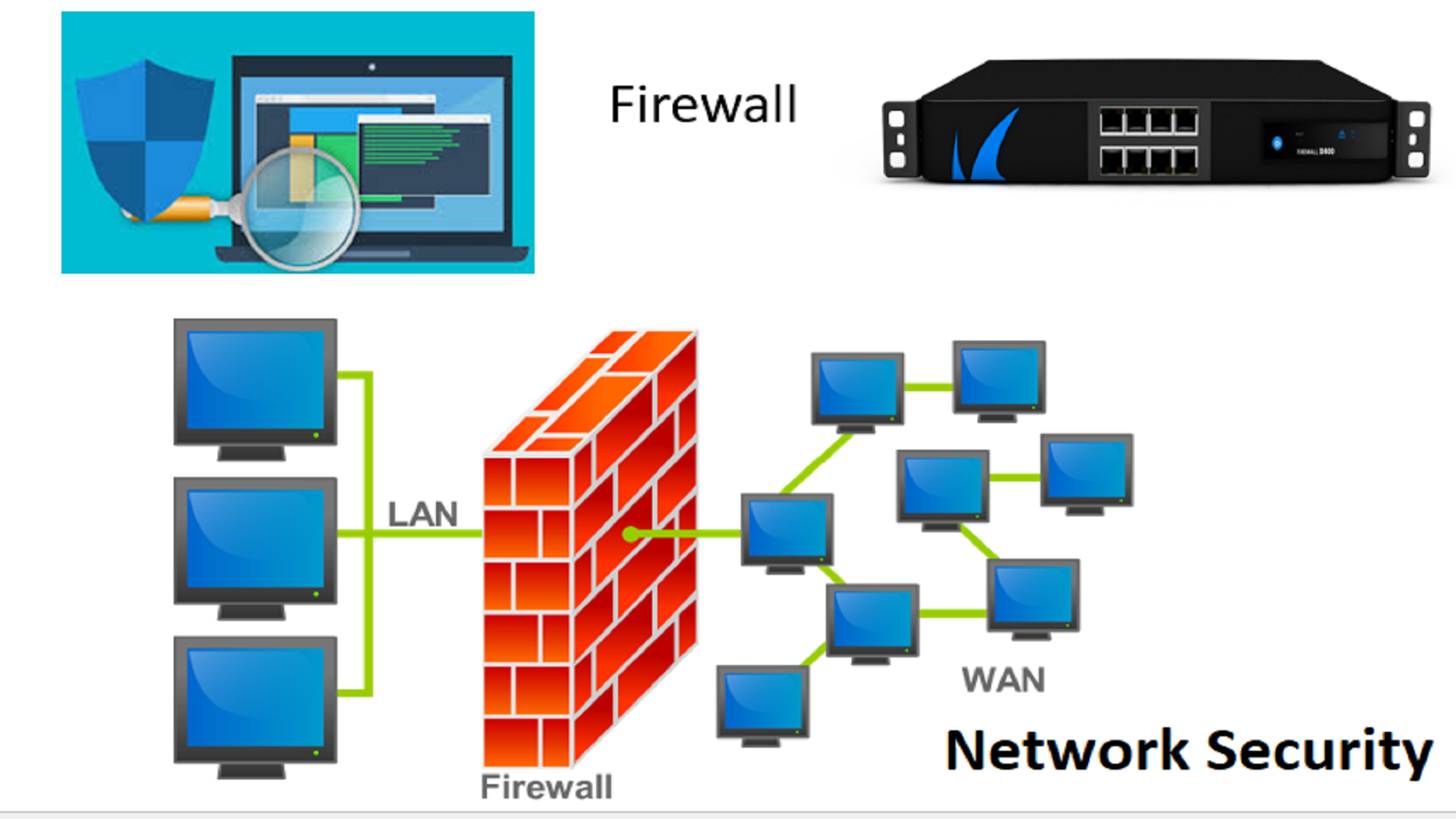
Remote IoT firewalls are advanced security solutions designed to protect networks and devices from unauthorized access and cyber threats. These firewalls function as a barrier between your IoT devices and the internet, filtering incoming and outgoing traffic to ensure only legitimate data passes through.
With the proliferation of IoT devices, the risk of cyberattacks has significantly increased. Traditional firewalls often fall short in addressing the unique security challenges posed by IoT ecosystems. Remote IoT firewalls, on the other hand, are specifically engineered to handle these complexities, offering enhanced protection for distributed networks.
Understanding IoT Firewalls
IoT firewalls differ from conventional firewalls in several ways. They are designed to monitor and manage the unique communication protocols used by IoT devices, ensuring seamless integration with existing network infrastructure. Additionally, they provide real-time threat detection and response capabilities, making them indispensable for modern cybersecurity strategies.
Why Remote IoT Firewalls Are Important
Remote IoT firewalls play a crucial role in securing networks and devices, particularly in environments where IoT devices are deployed across multiple locations. These firewalls offer several advantages, including:
- Centralized Management: Remote firewalls allow administrators to control and monitor network security from a central location, streamlining operations and reducing costs.
- Scalability: As your IoT network grows, remote firewalls can scale to accommodate additional devices and users without compromising performance.
- Advanced Threat Detection: With machine learning and artificial intelligence capabilities, remote IoT firewalls can identify and mitigate emerging threats in real-time.
Criteria for Selecting the Best Remote IoT Firewall
Choosing the right remote IoT firewall requires careful consideration of several factors. Here are some key criteria to evaluate:
Performance and Reliability
Ensure the firewall can handle the expected traffic load and maintain consistent performance under heavy usage. Look for solutions with proven track records in reliability and uptime.
Security Features
Assess the security features offered by the firewall, such as intrusion detection, encryption, and access control. These features are critical for protecting sensitive data and preventing unauthorized access.
Compatibility
Verify that the firewall is compatible with your existing network infrastructure and IoT devices. Seamless integration is essential for maximizing the firewall's effectiveness.
Top Remote IoT Firewall Examples
Here are some of the best remote IoT firewall examples currently available in the market:
1. Palo Alto Networks IoT Firewall
Palo Alto Networks offers a comprehensive IoT firewall solution that combines advanced threat prevention with deep visibility into IoT traffic. Its machine learning capabilities enable real-time threat detection and response, making it a top choice for enterprise-level security.
2. Fortinet FortiGate IoT Firewall
Fortinet's FortiGate IoT firewall provides robust security features, including intrusion prevention, application control, and secure sockets layer (SSL) inspection. Its scalable architecture makes it ideal for organizations of all sizes.
3. Check Point IoT Firewall
Check Point's IoT firewall solution offers unparalleled protection against advanced cyber threats. Featuring AI-driven threat prevention and unified security management, it is a powerful tool for securing IoT networks.
Biometric Integration in IoT Firewalls
Biometric authentication is increasingly being integrated into IoT firewalls to enhance security. By leveraging technologies such as fingerprint scanning, facial recognition, and voice identification, these firewalls provide an additional layer of protection against unauthorized access.
Benefits of Biometric Authentication
- Improved security through multi-factor authentication
- Enhanced user convenience with touchless authentication options
- Reduced reliance on passwords, minimizing the risk of credential theft
Comparing Key Features
When comparing remote IoT firewalls, consider the following key features:
Real-Time Monitoring
Real-time monitoring capabilities enable administrators to track network activity and detect anomalies instantly. This feature is essential for proactive threat management and minimizing downtime.
Automated Updates
Firewalls with automated update functionality ensure that security policies and threat signatures are always up-to-date, reducing the risk of vulnerabilities.
User-Friendly Interface
An intuitive user interface simplifies firewall management, allowing even non-technical users to configure and monitor security settings effectively.
Enhancing Network Security with IoT Firewalls
Implementing a remote IoT firewall is a critical step in enhancing network security. By filtering traffic, detecting threats, and controlling access, these firewalls help protect sensitive data and prevent cyberattacks.
Best Practices for Network Security
- Regularly update firewall firmware and security policies
- Conduct periodic security audits to identify vulnerabilities
- Implement strong authentication mechanisms for all users and devices
Implementation Best Practices
Successfully implementing a remote IoT firewall requires adherence to best practices. Start by conducting a thorough assessment of your network infrastructure to identify potential security gaps. Then, follow these steps:
Plan and Design
Create a detailed implementation plan, outlining the firewall's configuration, deployment strategy, and integration with existing systems.
Test and Validate
Perform rigorous testing to ensure the firewall functions as intended and meets your security requirements. Validate its performance under various scenarios to confirm reliability.
Monitor and Maintain
Continuously monitor the firewall's performance and security effectiveness. Regular maintenance ensures it remains aligned with evolving security threats and business needs.
The Future of Remote IoT Firewalls
The future of remote IoT firewalls looks promising, with advancements in artificial intelligence, machine learning, and cloud computing driving innovation. These technologies will enable even more sophisticated threat detection and response capabilities, further enhancing network security.
Trends to Watch
- Increased adoption of AI-driven security solutions
- Growing emphasis on zero-trust architecture for IoT networks
- Development of unified threat management platforms for IoT ecosystems
Conclusion and Call to Action
In conclusion, remote IoT firewalls are essential tools for safeguarding your network and IoT devices from cyber threats. By selecting the right firewall and implementing best practices, you can significantly enhance your network security and protect valuable assets.
We encourage you to share your thoughts and experiences with remote IoT firewalls in the comments section below. Additionally, feel free to explore our other articles on cybersecurity and IoT technologies for more insights and guidance.